GCP IAM Roles: All types and recommended setup

Rom Carmel
May 22, 2024
Google Cloud Platform (GCP) is one of the world’s most widely used cloud services. At the heart of this system lies roles, which act as predefined sets of permissions that grant users specific access levels amidst the complexity of credentials, identities, and resources in the cloud environment.
74% of data breaches originate from the misuse of privileged credentials, which is why it’s so critical to learn the ins and outs of GCP IAM roles and add an additional layer of protection to your data and services.
What are GCP IAM Roles?
Google Cloud Platform (GCP) Identity and Access Management (IAM) roles are a fundamental component designed to help manage access control and permissions within GCP environments. These roles are collections of permissions that determine what actions an identity (a user, group, or service account) can perform on GCP resources.
IAM roles provide a flexible and secure way to manage who has access to GCP resources and what actions they can perform, ensuring that only authorized individuals can access sensitive data and perform operations within a GCP project.
Three Types of GCP IAM Roles
Effectively managing IAM roles is crucial for securing GCP environments against unauthorized access and potential security breaches. By understanding the structure and purpose of these roles, your organization can implement robust access control policies (often outlined as a critical part of any good IT security policy) that protect resources while facilitating smooth operations across cloud environments.
GCP IAM roles are categorized into three main types: Basic, predefined, and custom.
Basic Roles
Basic roles, formerly known as ‘primitive roles,’ are the most broad and straightforward options available. These roles encompass a vast array of permissions spanning multiple Google Cloud services, granting users extensive access within a project. The three primary basic roles are:
- Owner: Grants complete control over a project, including the ability to manage roles, permissions, and billing settings.
- Editor: Permits modification and creation of resources within a project, excluding certain sensitive operations.
- Viewer: Grants read-only access to resources, enabling users to view but not alter existing data or configurations.
While basic roles offer unparalleled simplicity, their far-reaching permissions can pose significant security risks if misused. As a general guideline, it is advisable to reserve basic role assignments for testing or sandboxed environments and avoid their use in production scenarios involving sensitive data.
Predefined Roles
Predefined roles offer a balanced approach to access control. These roles provide granular access to specific Google Cloud services, ensuring users receive only the permissions necessary to perform their assigned tasks. By adhering to the principle of least privilege, predefined roles enhance security, identity governance, and reduce the risk of unintended data exposure or resource misuse.
For example, the BigQuery service offers predefined roles such as BigQuery Admin, BigQuery Data Owner, and BigQuery Job User, enabling precise access control for various data management tasks.
One key advantage of predefined roles is their seamless integration with Google Cloud’s evolving feature set. As new services or capabilities are introduced, Google automatically updates the corresponding predefined roles with the necessary permissions, ensuring users remain empowered with the latest access privileges without manual intervention.
Custom Roles
Custom roles emerge as a powerful solution when predefined roles fail to meet your organization’s specific requirements and evolving cyber threats. Custom roles enable administrators to meticulously curate a unique set of permissions, granting users access to only the resources and actions they genuinely require.
The creation of custom roles is a two-fold process. First, your organization must identify the specific permissions needed for a particular task or job function. Then, you can bundle these permissions into a custom role, ensuring a precise and tailored access control mechanism.
While custom roles offer unparalleled flexibility, they also introduce additional complexity and maintenance overhead. Your organization must diligently monitor and update custom roles as new permissions or services are introduced, ensuring their continued relevance and effectiveness.
GCP IAM Roles: 6 Steps for a Seamless Setup
The following steps outline a streamlined approach to configuring IAM roles on GCP.
- Log into your Google Cloud Console. This is the web interface where you can manage all aspects of your GCP resources.
- Navigate to the IAM & Admin section on the dashboard. This area is dedicated to identity and access management, where you can oversee roles, permissions, and the organizational structure of your resources.
- Learn the hierarchy of GCP resources. GCP organizes resources into projects, folders, and organizations. This hierarchy influences how IAM roles are inherited and applied. It’s crucial to understand this structure as it will dictate how you assign roles at different levels (project, folder, or organization) to meet your access control requirements.
- Identify the roles that suit your needs. GCP offers a wide range of predefined roles, each encapsulating a set of permissions designed for specific tasks within the platform. These roles range from broad (Owner, Editor, Viewer) to service-specific (e.g., Compute Admin, Storage Object Admin). Assess the responsibilities of your team members and select the roles that best match their needs. If necessary, you can also create custom roles with a tailored set of permissions.
- Assign the appropriate roles. In the IAM & Admin section of the Google Cloud Console, navigate to the IAM page. Here you can add members (users, groups, and service accounts) and assign them roles. When adding a member, you’ll enter their email address and select the role from a dropdown menu. It’s important to apply the principle of least privilege—only grant the permissions necessary for users to perform their tasks. Optionally, for more advanced scenarios, consider setting up conditional IAM policies. These policies allow you to specify conditions under which the assigned roles are effective. For example, you might restrict certain actions to specific IP ranges or times of day. This adds an extra layer of security and control over how and when your cloud resources can be accessed.
- Regularly review and audit your IAM settings. GCP provides tools for monitoring access logs and analyzing permissions. Use these tools to ensure that only authorized users have access and use their permissions responsibly. Regular audits and risk assessments help maintain a secure and efficient access management system by identifying unused roles or overly permissive settings that could be tightened.
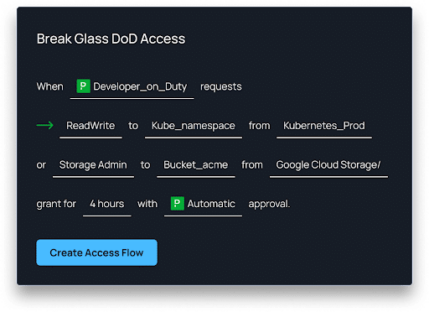
Using Apono with GCP IAM Roles
Mastering the art of role assignment within Google Cloud Platform’s Identity and Access Management framework is a critical endeavor for organizations seeking to strike the perfect balance between security and operational efficiency. By understanding the nuances of basic, predefined, and custom roles, organizations can meticulously tailor access privileges to align with their unique requirements and risk profiles.
Embracing principles such as least privilege, separation of duties, and periodic access reviews can help you cultivate a secure and well-governed environment with seamless integration with identity providers and robust logging and monitoring capabilities. Within this context, Apono can significantly enhance the management of GCP IAM roles, offering a layer of automation and oversight that simplifies the complexities of permissions management.
Apono integrates seamlessly with GCP IAM, giving administrators a more intuitive and granular control over roles and permissions. Using Apono, you can automate the assignment and revocation of IAM roles based on user activities, job functions, or defined policies. This feature reduces the administrative burden and minimizes the risk of human error, ensuring that only the right individuals have access to sensitive resources at the right time. Moreover, Apono’s capabilities extend to monitoring and auditing, giving teams clear insights into permissions usage and anomalies, which is critical for compliance and security governance.
Get started with Apono for free.