Apono integration for Grafana: Enabling Just-in-Time access for data sources
Brad Boggess
March 9, 2026

For many organizations, Grafana is a central operational system. Engineers use it to investigate issues, analyze logs, review infrastructure metrics, and query production-connected databases. But while dashboards are visible, the real sensitivity lies in the underlying data sources Grafana connects to.
These data sources often include systems such as logs stored in Elasticsearch or OpenSearch, SQL databases like PostgreSQL or MySQL, and Amazon CloudWatch metrics. Access to these systems can provide visibility into production telemetry, infrastructure performance, and potentially sensitive operational data.
The challenge is clear: How do you give engineers fast access to Grafana data sources without maintaining standing, over-privileged access?
The problem: static access in dynamic environments
In standard operating environments, Grafana data sources are typically accessed via long-lived IAM roles or broad group assignments. This “always-on” model is designed for speed, ensuring engineers have immediate visibility during critical incidents without the friction of authentication and authorization delays.
However, for organizations handling highly sensitive data or operating under strict regulatory constraints, this approach can introduce unique operational challenges, such as:
- Persistent permissions may exceed the actual window of time an engineer needs to perform a task.
- Distinguishing between routine monitoring and targeted investigative access can become difficult during compliance reviews.
- Compliance and audit friction.
For these specialized scenarios, teams are moving toward a Just-in-Time access model. This allows for a security posture that remains dormant by default and activates only when a specific, verified need arises, aligning high-stakes security with operational flow.
Governing Grafana data sources with Just-in-Time access
Apono integrates with Grafana to continuously discover configured data sources. Each discovered data source becomes a governed resource within Apono’s access control framework.
Security and platform teams define policies to specify:
- Who can request access
- Which data sources they can access
- Whether human approval is required
- Maximum access duration
- Contextual conditions (such as on-call status)
Instead of granting permanent access to a logs or metrics data source, organizations move to an on-demand model.
A typical workflow
- An engineer needs to query a specific Grafana data source (for example, a logs or metrics backend).
- They submit a request for access.
- Apono evaluates the request against predefined policies, and user and asset context.
Access is granted for a defined time window. - When the time expires, access is automatically revoked.
There are no permanent role changes and no lingering privileges. Access becomes scoped, time-bound, and policy-driven.
Reference architecture: Just-in-Time access for Grafana data sources
The diagram below illustrates how Apono integrates with Grafana and connected data sources to enforce time-bound access while preserving operational workflows.
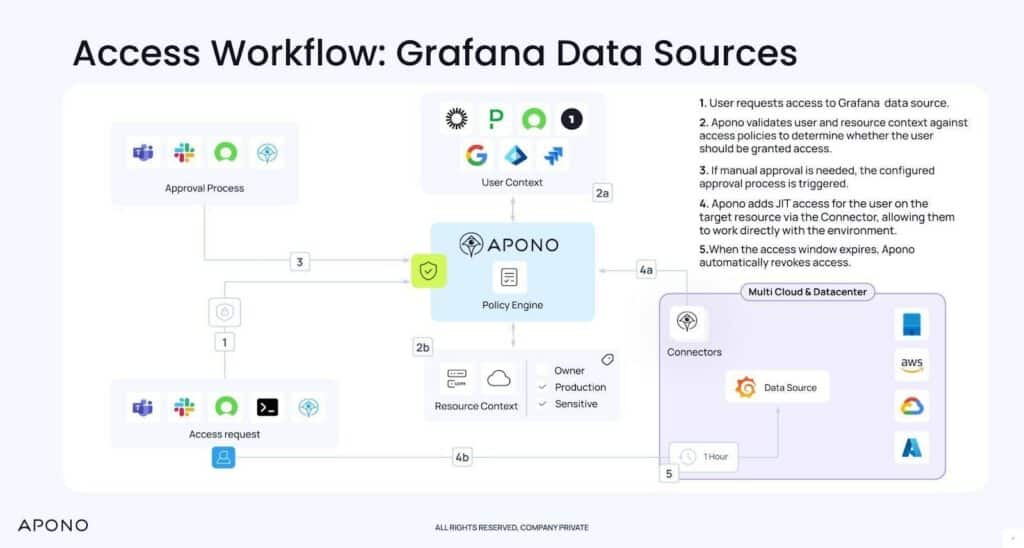
In this model:
- Grafana connects to multiple data sources (logs, metrics, traces, cloud services, databases).
- Apono integrates with Grafana to discover and govern access to those data sources.
- Access requests are evaluated against centralized policies.
- Permissions are provisioned temporarily and revoked automatically.
This architecture ensures that access to observability data is dynamic and controlled, rather than static and persistent.
Incorporating operational context with Grafana Cloud IRM
For teams using Grafana Cloud IRM, access decisions can incorporate operational signals such as:
- On-call schedules
- Active incident participation
- Responder roles
By integrating Grafana Cloud IRM with Apono, organizations can align access with real-time operational responsibility. For example:
- Only an engineer currently on call can receive immediate access to a production data source.
- Access can be limited to the duration of an active incident.
- Permissions automatically expire when responsibility shifts or the incident is resolved.
This ensures access reflects real-time operational context rather than static IAM group membership.
Benefits for users
Organizations using Grafana together with Apono report improvements across both security and operational efficiency. Here’s a closer look at the benefits:
- Zero Standing Privileges: Access to Grafana data sources is granted only when required and automatically revoked.
- Faster investigations: Engineers obtain faster access without waiting for manual IAM updates.
- Reduced blast radius: Short-lived permissions limit exposure if credentials are compromised.
- Policy-driven governance: Access policies are centrally defined and consistently enforced.
- Full audit visibility: Every access event is logged, supporting compliance and review processes.
Getting started and next steps
The Apono integration is available for both on-premises Grafana and Grafana Cloud.
As a practical first step, we recommend identifying which of your Grafana data sources connect to sensitive production systems and are currently governed by standing roles.
From there, teams can:
- Integrate Grafana with Apono
- Discover existing data sources
- Define time-bound access policies
- Gradually remove permanent access assignments
As observability environments grow in scale and importance, implementing Just-in-Time and least privilege access for Grafana data sources helps minimize risks without slowing teams down.
To learn more, please explore our integration documentation.