Zero Standing Privileges Should Be The Bar Everyone Sets
The best way to secure your cloud environment is to shrink your attack surface—make elevated privileges temporary by default and adopt least privilege. Apono lets you apply Just-in-Time, Just-Enough access across clouds, Kubernetes, databases, and more from a single policy plane, reducing risk for every user, machine, and AI agent.

Trusted by Security, IAM and DevOps Teams
The Problem
Challenges to Achieving Zero Standing Privilege
Fragmented Visibility
40,000+ cloud permissions across AWS/Azure/GCP make “who has what” opaque.
Standing Privileges
94–96% privileges unused, expanding attack surface with zero ROI
NHI Sprawl
Non-Human Identities outnumber humans ~150:1, multiplying secret exposure and attack paths.
Static Roles
Pre-created roles cannot keep up with constant change in cloud
Remediation Paralysis
99% of identities are overly permissive. Fear of breakage keeps excess in place.
Manual Approval Bottlenecks
Ticket queues delay elevation and inflate MTTR by 50%.
Auditability Requirements
Auditors need end-to-end elevation logs; fragmented tooling makes that hard.
Privilege Bloat
~50% high-risk; over-scoped identities widen blast radius.
The problem
Turn Chaos into Controlled Access
Watch standing access rights become least-privileged. With Apono, access is time-bound, context-based, and fully logged, empowering engineers to innovate faster.
Solution
Zero Standing Privilege, Cloud-Wide
Replace always-on permissions with Just-in-Time, Just-Enough access governed by adaptive policies. Shrink attack surface and blast radius while engineers get the right access in seconds, with end-to-end audit to sustain ZSP at scale.

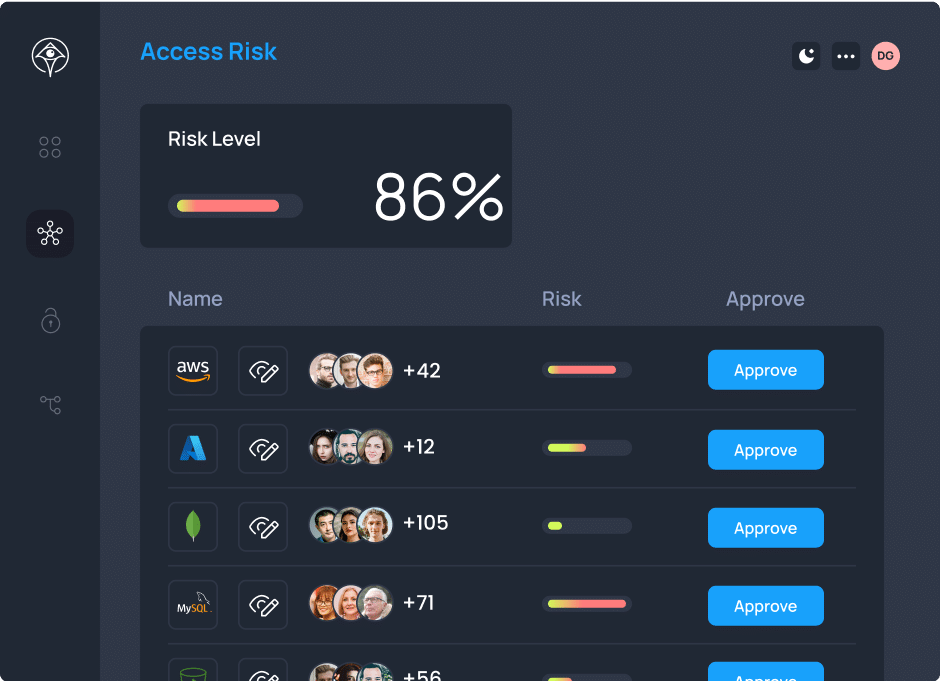
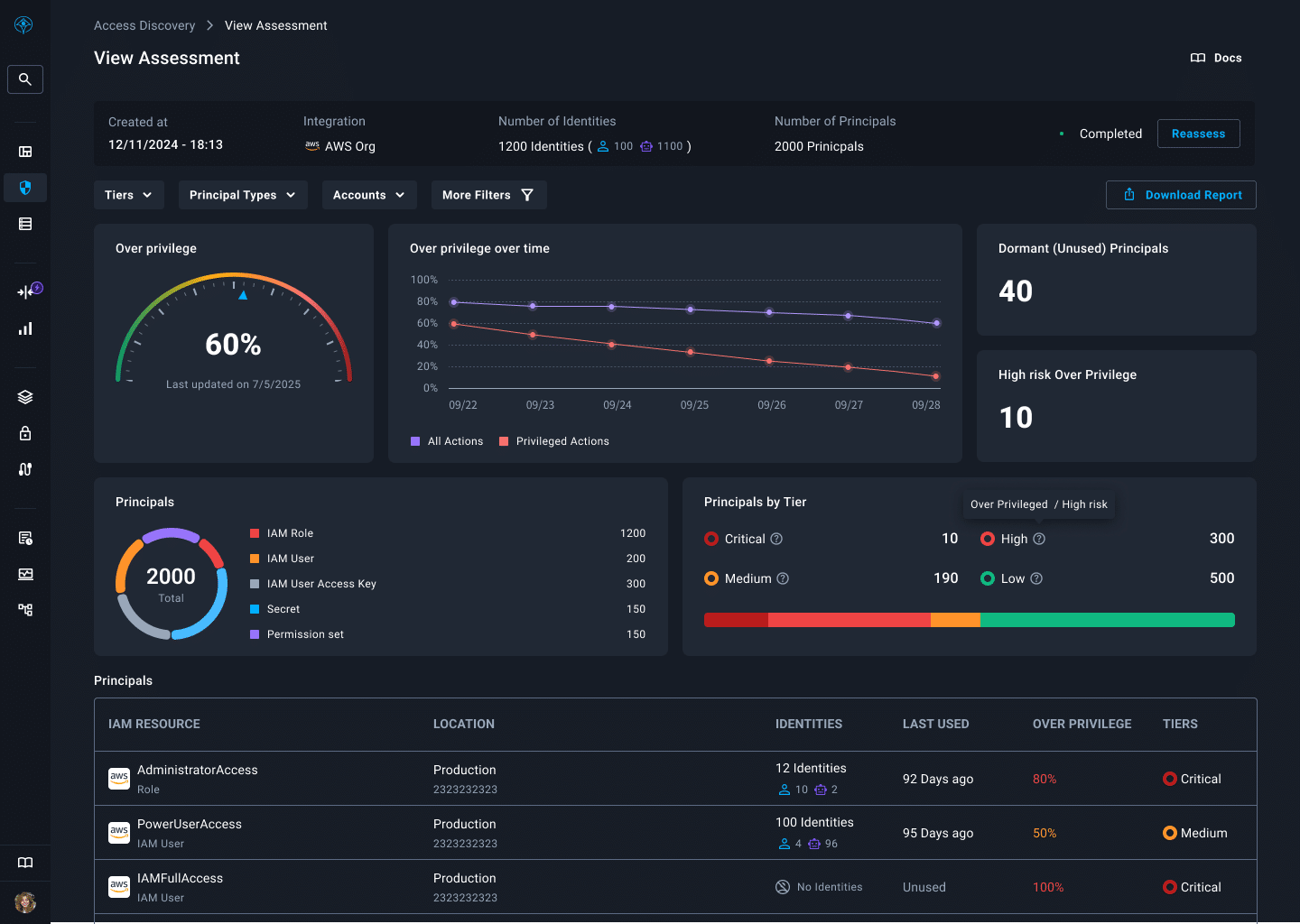
Identify Overprivilege. Then Eliminate It.
Contextualize who has what access with how it’s actually used and how sensitive it is, surfacing dormant and excessive access everywhere. With Access Discovery, you can easily identify all existing privileges, quarantine zombie accounts, and prioritize remediation.
Get Started


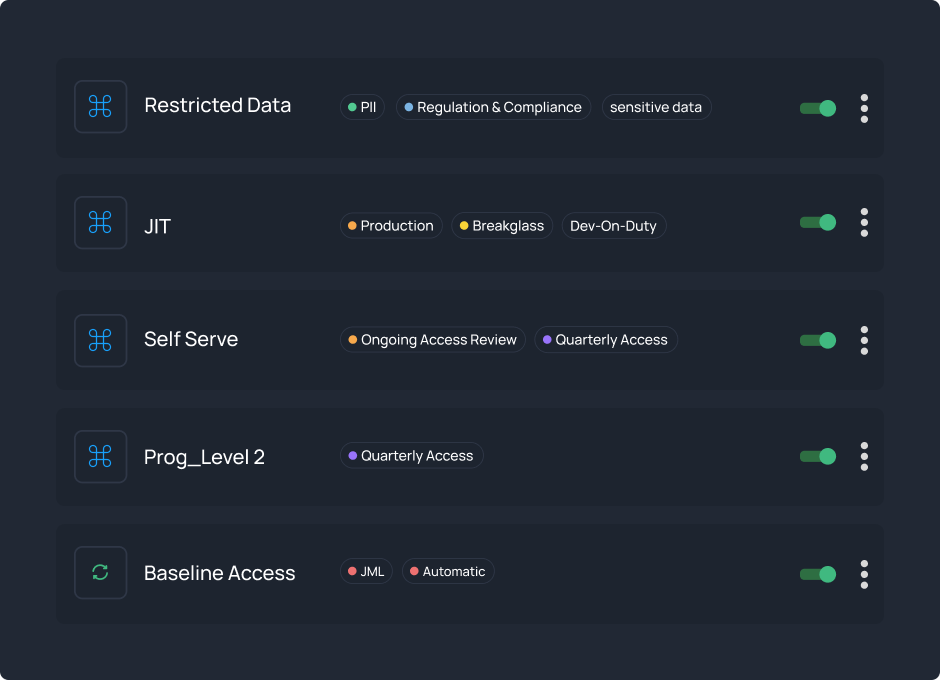
Enforce Zero Standing Privilege, Everywhere
Access Flows operationalize your policies with granular precision, then issue Just-in-Time, Just-Enough access with auto-revoke and full audit. Engineers get the proper access in seconds, not ticket cycles, while you maintain Zero Standing Privileges by default.
Get Started
Prove Control, Streamline Audits
Every request, approval, grant, and revocation is logged end-to-end with anomaly alerts and evidence on demand. Clear metrics provide continuous assurance, facilitate easier reviews, and result in cleaner audits.
Get Started
How Customer Teams Achieve Zero Standing Privileges with Apono
What are standing privileges and why are they risky?
What is Just-In-Time Access?
Standing privileges are always-on permissions that never expire, even when not actively needed.
- Create permanent attack vectors that hackers can exploit 24/7
- Enable lateral movement if any single account is compromised
- Accumulate over time as employees change roles but keep old access (privilege sprawl)
- Expand blast radius from 1 compromised account to entire infrastructure
Learn about standing privilege risks
What is Zero Standing Privilege (ZSP)?
Zero Standing Privilege is a security model where no user has permanent administrative access to critical systems.
- All privileged access is temporary and provisioned Just-in-Time and Just-Enough
- Permissions automatically expire after use or specified duration
- Reduces attack surface by eliminating always-on privileged accounts
- Reduces the blast radius by removing excessive, sensitive privileges
- Achieves least privilege principle at scale across cloud infrastructure
Explore ZSP best practices
How does Apono achieve Zero Standing Privileges?
Apono replaces permanent access with temporary, fully-audited Just-in-Time and Just-Enough permissions that automatically expire.
- Convert static IAM roles into dynamic, ephemeral Access Flows
- Grant permissions only when needed, for exactly the time necessary
- Automatically revoke access when time expires or task completes
- Intelligently assist in reducing excessive privileges without interrupting workflows
- Maintain emergency break-glass access without standing privileges
See how teams achieve ZSP
What's the difference between Zero Trust and Zero Standing Privileges?
While Zero Trust assumes no implicit trust, Zero Standing Privileges specifically eliminates permanent admin
- Zero Trust: Verify every request regardless of source
- ZSP: Remove all persistent privileged access
- Both work together: Zero Trust architecture with ZSP implementation
- Apono enables both through Just-in-Time, verified, temporary access
Read about modern access security
What's the actual risk reduction we can expect?
Most organizations see 94-96% reduction in attack surface within the first month.
- 94% smaller blast radius from any potential breach
- 50% faster incident response with clear access audit trails
- Zero standing access to production databases and crown jewels
View the full platform comparison
How do you handle emergency and break-glass access?
Emergency access is granted instantly while maintaining Zero Standing Privileges.
- Validates break-glass requests with incident tickets for secure, automatically approved access that reduces MTTR
- Break-glass workflows activate in under 10 seconds
- Full audit trail of who accessed what and why
- Automatic revocation after incident resolution
- Risk-based approval routing for different emergency types
Learn about break-glass protocols
How Can we implement ZSP gradually or does it require a big-bang approach?
Start with your highest-risk resources and expand gradually.
- Begin with production databases or cloud admin roles
- Use Access Discovery to identify and prioritize excessive privileges
- Convert one team or service at a time to JIT access
- Most customers achieve full ZSP across their environment in 4-6 weeks
Get started with Access Discovery