Agentic AI Risk Survey: Why CISOs Are Slowing Adoption

Gabriel Avner
February 26, 2026

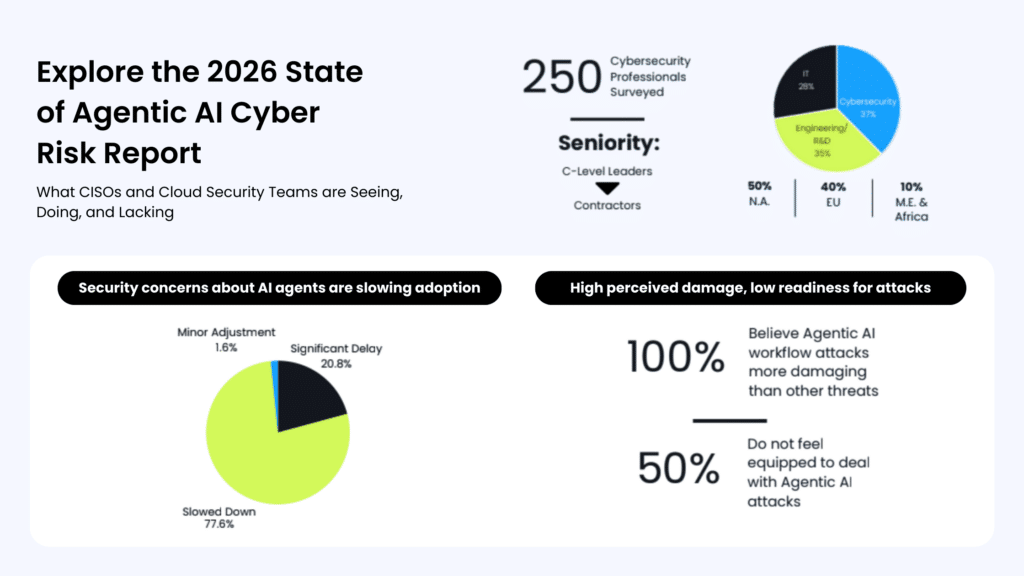
This week, we released our 2026 State of Agentic AI Risk Report, a global survey of 250 senior cybersecurity leaders examining how enterprises are approaching agentic AI as it moves closer to production.
The findings point to a clear reality. While AI agents are advancing quickly, security leaders are deliberately slowing adoption. In fact, 98% of respondents say security and data concerns have already slowed deployments, added scrutiny, or reduced the scope of agentic AI initiatives.
This is not resistance to innovation. It is a response to risk.
A Different View From the Security Seat
To product and engineering teams, agentic AI represents acceleration. Agents can deploy infrastructure, triage incidents, modify configurations, and interact directly with production systems. The productivity upside is undeniable.
From the CISO’s perspective, the question is different: what happens when autonomous systems inherit today’s privilege sprawl?
In our study, 100% of respondents agreed that an attack targeting agentic AI workflows would be more damaging than a traditional cyberattack. That level of alignment reflects a shared understanding that automation multiplies both efficiency and impact.
If a human with excessive privileges can cause damage, an autonomous system with the same privileges can do so faster and at greater scale.
A Real-World Warning of Agentic AI Risk
Recent events have reinforced those concerns.
According to reporting by Engadget, a 13-hour AWS outage was reportedly triggered by Amazon’s own internal AI tools making unintended changes to production systems. Regardless of the technical specifics, the lesson is clear. When AI-driven systems operate directly in live environments without tightly scoped guardrails, the consequences can ripple quickly.
For CISOs, this was not surprising. It validated what many already believed: autonomous systems are not just another application layer. They are actors with privileges. And poorly governed privileges create outsized risk.
The Preparedness Gap
The slowdown in adoption becomes clearer when viewed through a readiness lens.
Only 21% of organizations in our study say they feel prepared to manage attacks involving agentic AI or autonomous workflows. That gap between ambition and operational readiness is fueling concern around agentic AI risk at the executive level.
Security leaders are not evaluating AI in isolation. They are assessing it against environments already strained by accumulated privilege and fragmented visibility. Over time, human and non-human identities have accrued access well beyond actual usage. Cloud policies are scattered across platforms. Standing permissions persist long after their purpose has expired.
Within that reality, agentic AI risk is not hypothetical. It is structural.
Autonomous agents operate at machine speed. When introduced into environments burdened with excessive standing access, they amplify the impact of every overprivileged role and every blind spot in visibility. The blast radius does not grow incrementally. It expands exponentially.
Agentic AI does not create entirely new categories of risk. It accelerates and scales the identity and access weaknesses that already exist.
That is the foundation CISOs are being asked to trust.
What CISOs Are Actually Asking For to Reduce Agentic AI Risk
The hesitation we’re seeing is not about stopping AI adoption. It is about redefining the privilege model that supports it.
Security leaders recognize that agentic AI risk is not just a model accuracy issue. It is an access issue. When autonomous systems operate with standing privileges, the blast radius expands exponentially.
CISOs are looking for a structural shift in how access is granted and governed. The conversation is moving from patching entitlements to redesigning guardrails.
At a strategic level, that shift looks like this:
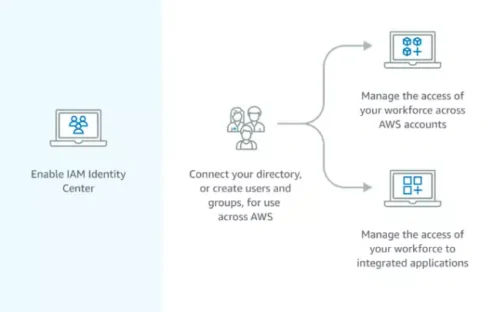
- From standing privilege to just-in-time, task-bound access
- From static, pre-created roles to dynamic controls that understand intent
- From fragmented IAM systems to unified governance across human and non-human identities
- From broad permissions granted for convenience to scoped access aligned to sensitivity and risk
This is not a tooling adjustment. It is a mindset change.
Agents should not inherit permanent authority. They should operate within clearly defined boundaries, receiving the minimum access necessary to complete a defined objective, with automatic revocation built in.
When those guardrails are in place, autonomy becomes sustainable. Without them, caution is not only rational, it is responsible.
A Pivotal Moment
Agentic AI is forcing organizations to confront identity and privilege gaps that have existed for years. The difference now is speed. What was previously manageable human risk becomes amplified when systems can act independently and continuously.
The friction reported by 98% of respondents between accelerating AI adoption and meeting cybersecurity priorities is not a philosophical disagreement. It is a signal that legacy privilege models were not built for autonomy.
Organizations that invest now in reducing standing privileges and implementing dynamic, intent-aware access controls will be positioned to move forward with confidence. Those that do not will continue to hesitate as AI initiatives approach production.
The agentic future is not on hold. It is waiting for the right guardrails.
Ready to Benchmark Your Agentic AI Risk?
The 2026 State of Agentic AI Risk Report reveals:
- Where security leaders feel most exposed
- The identity gaps slowing AI deployment
- How prepared organizations are to manage agentic AI risk
- The access model shifts CISOs are prioritizing now
If AI agents are entering your environment this year, your privilege model must evolve with them.