9 Must Have Components for a Privileged Access Management Audit

The Apono Team
November 11, 2025
Privileged accounts are often treated as background plumbing until something goes wrong. They sit across cloud consoles, databases, and pipelines and have the power to alter configurations or bring production to a halt, making them a favorite target of bad actors.
Credential theft surged 160% in 2025, making stolen identities one of the fastest-growing attack vectors. When those stolen credentials belong to privileged accounts, the exposure isn’t limited to one system; it can spread across the whole environment.
A privileged access management audit is one of the few ways to pressure-test your organization’s ability to withstand this reality: identifying where privileged access lives, how it’s controlled, and whether the guardrails actually hold when it matters.
What is a privileged access management audit?
A Privileged Access Management (PAM) audit is a structured review of how your organization grants, monitors, and controls elevated access. Unlike general access reviews, it focuses on the most sensitive accounts, such as administrators, database owners, CI/CD pipelines, and cloud root credentials, which, if misused, can lead to breaches and compliance failures.
From a compliance standpoint, a PAM audit demonstrates your organization’s adherence to frameworks like SOC 2, HIPAA, GDPR, and CCPA, which all require strict controls over privileged access. On the security side, the audit identifies risky standing permissions, unused or over-privileged accounts, and gaps in access governance that could be exploited in identity-based attacks such as credential theft or insider misuse.
PAM differs from Identity and Access Management (IAM) audits. IAM reviews look across the workforce to determine role appropriateness. PAM audits go deeper into the highest-risk accounts where a single misconfiguration can lead to lateral movement or critical outages.

Non-Human Identities: The Hidden Majority in PAM Audits
In modern cloud and SaaS environments, non-human identities (NHIs)—service accounts, API keys, machine identities, bots, and agents— outnumber human identities by 80:1. This proliferation introduces a lack of visibility over stale, long-lived tokens and over-privileged service accounts. When compromised, an NHI can be abused to conduct malicious activities, from exfiltrating data to moving laterally across systems and triggering destructive agent-to-agent chains. It’s more critical than ever to treat NHIs with the same rigour as human admins, such as moving NHIs from static, long-lived keys into automated Just-in-Time (JIT) and Just-Enough Privileges (JEP) flows.
5 Key Objectives of a Privileged Access Management Audit
A PAM audit tests whether access models can withstand real-world pressure, with five key goals.
1. Identify all Privileged Accounts
The starting point is a complete inventory of privileged accounts across infrastructure, SaaS, and hybrid environments. Shadow admins and dormant credentials often go unnoticed but can be exploited as entry points. Don’t forget that a complete inventory eliminates blind spots and extends to non-human identities, which often lack MFA or visibility but can be abused as powerful entry points.
2. Assess Least Privilege Enforcement
Auditors examine whether access is restricted to the minimum required, both in scope and time. Standing privileges or overly broad entitlements signal persistent risk, even if they are rarely used. The test is whether the least privilege is enforced in daily operations, not just written in policy.
3. Validate Authentication and Approval Workflows
How access is granted matters as much as who receives it. Auditors review whether workflows include measures such as multi-factor authentication, just-in-time approvals, and human oversight, and whether these steps are consistently applied.
4. Confirm Monitoring and Logging
Privileged activity must be traceable. Auditors look for detailed, tamper-resistant logs that link actions to specific identities and preserve enough context to support investigations. Strong logging is the foundation of accountability.
5. Ensure Compliance Alignment
Another tick-box for auditors is whether privileged access controls map directly to frameworks like SOC 2 and GDPR. This step is about demonstrating that practices meet external requirements, not just internal expectations.

9 Must-Have Components For a Privileged Access Management Audit
Here’s what auditors and regulators look for when assessing whether privileged access is secure and accountable.

1. Comprehensive Inventory of Privileged Accounts
Most organizations underestimate the number of privileged accounts in their environment. Privileged identities go beyond administrators in hybrid setups spanning SaaS platforms, cloud services, and legacy infrastructure. They include NHIs like API tokens and machine accounts, which rarely rotate credentials and fall outside the visibility of central IAM oversight.
Why it matters: Forgotten or orphaned accounts are common targets for attackers, since they often lack MFA or monitoring.
Auditors look for: A dynamic inventory that is continuously updated, not a static spreadsheet compiled ahead of an audit.
Best practice: Automate discovery and classification to identify all privileged identities, and assign a clear owner for each account’s lifecycle. Using a cloud-native access management platform provides continuous discovery across cloud and SaaS environments, making privileged identities visible and traceable.
2. Verification of Least Privilege Enforcement
Enforcing least privilege is one of the most complex parts of PAM and applies to human and non-human identities. Developers and administrators often accumulate entitlements beyond their needs over time. A PAM audit examines whether permissions are limited in scope, time-bound, and automatically revoked.
Why it matters: Standing privileges remain risky even when accounts are idle.
Auditors look for: Proof that access is temporary and scoped, including just-in-time provisioning, role-based permissions, and consistent automated revocation.
Best practice: Retire static admin groups for contextual, time-limited roles. Monitor exceptions closely to prevent privilege creep, which keeps security controls practical for engineering teams while reducing long-term exposure. Additionally, machine identities should be scoped to task-specific, short-lived permissions under a JEP model.
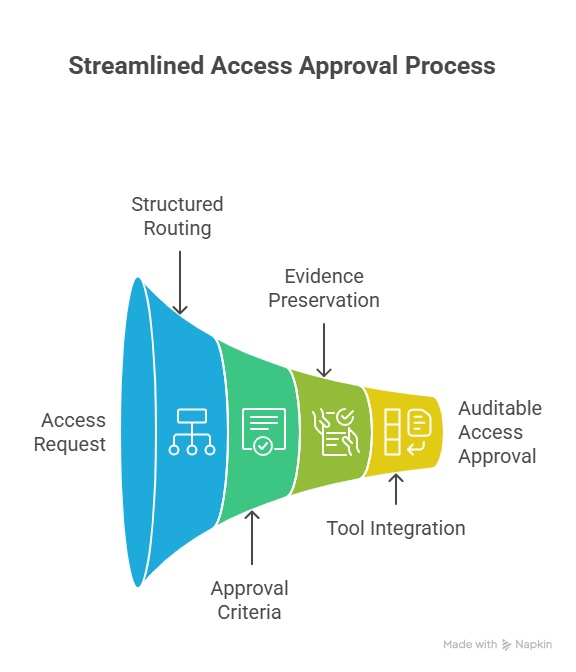
3. Access Request and Approval Workflows
Privileged access needs to follow a clear, documented process. Ad hoc approvals over email or chat leave no reliable record and create gaps in accountability. Auditors determine whether requests are routed through structured channels, with approval criteria defined and evidence preserved for review.
Why it matters: Informal workflows make access decisions opaque and vulnerable to mistakes or bias.
Auditors look for: Request trails that record who requested access, who approved it, and why. Multi-factor approvals are now standard for high-risk requests.
Best practice: Integrate access workflows into the tools engineers already use. Approvals through Slack, Teams, or CLI allow teams to move quickly while leaving an auditable trail.
4. Session Monitoring and Logging
Once privileged access is granted, organizations need complete visibility into its use. PAM audits assess whether sessions can be reconstructed in detail, including logins and the commands executed, configurations changed, and data accessed.
Why it matters: Without detailed logs of privileged sessions, organizations lose both forensic evidence and accountability.
Auditors look for: Tamper-resistant logs tied to individual identities rather than shared accounts, and centralized for consistent retention and review.
Best practice: Route privileged activity logs into SIEM or SOAR platforms for correlation and alerting. Run regular spot checks to confirm accuracy so the data supports investigations and ongoing operations.
5. Automated Access Expiration and Revocation
Revoking access manually is error-prone. Under pressure, administrators often overlook accounts after projects close or roles change. PAM audits check whether expiration is built into the system by default.
Why it matters: Dormant accounts are a common attack vector. If unused rights remain active, they also contradict least-privilege principles.
Auditors look for: Expiration policies applied to human and machine identities, with revocation tied to triggers such as session end, project completion, or HR system updates.
Best practice: Use automated policies that enforce time-bound access. Schedule periodic reviews to catch exceptions or drift. Automation reduces the chance of oversight and keeps privileges aligned with actual need.
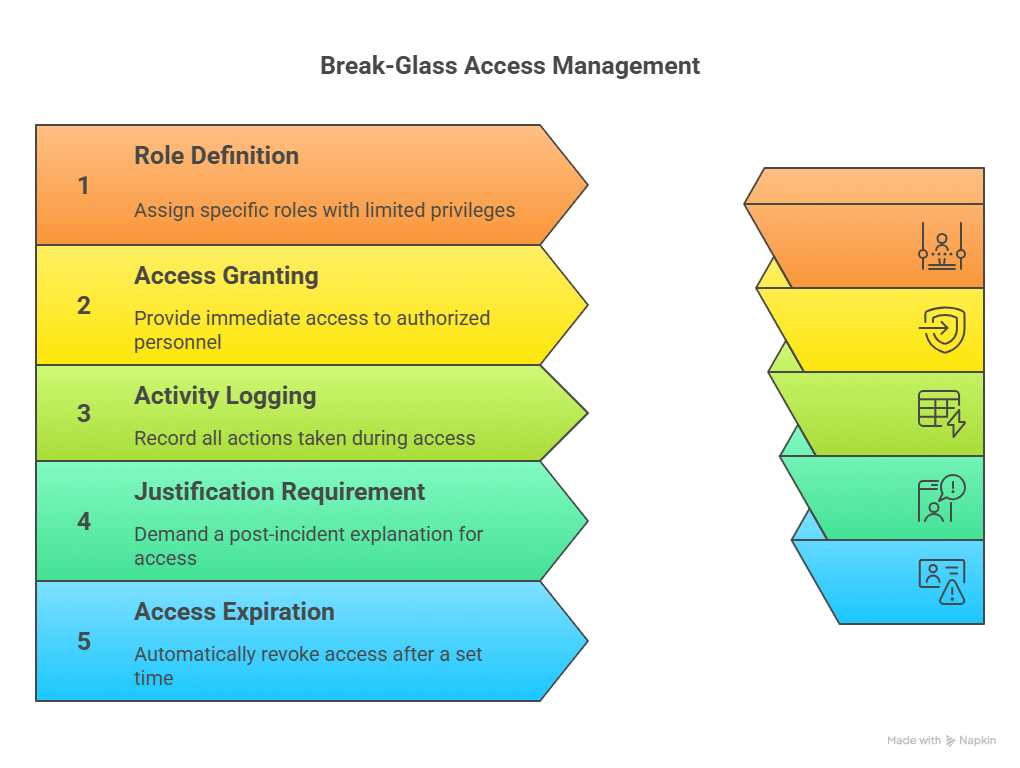
6. Break-Glass and On-Call Access Mechanisms
Outages and security incidents sometimes require immediate intervention. Break-glass mechanisms give engineers rapid access in those moments while keeping the activity logged and accountable.
Why it matters: High-pressure situations can lead teams to cut corners. Without structured emergency flows, organizations resort to insecure workarounds.
Auditors look for: Documented policies for break-glass use, detailed logs of each event, and retroactive approvals or justifications. They also expect access to be narrowly scoped and time-limited.
Best practice: Define emergency roles with limited privileges, require post-incident justification, and set automatic expiration. This best practice keeps response times fast while ensuring access remains auditable.
7. Compliance Alignment and Reporting
PAM controls must align with (and provide evidence for) established frameworks like SOC 2, HIPAA, GDPR, and ISO 27001.
Why it matters: Demonstrating compliance is often as critical as preventing breaches. Regulators, customers, and partners expect clear proof that privileged access is governed appropriately, supported by robust cloud security controls.
Auditors look for: Reports that link specific controls to compliance clauses, supported by evidence.
Best practice: Automate reporting so compliance data is produced continuously, rather than assembled only at audit time, which makes audit readiness part of daily operations.
8. Continuous Monitoring for Anomalous Behavior
PAM audits now look beyond static controls to how organizations detect anomalies, such as an API key suddenly accessing new regions or service accounts running commands outside their normal workflow.
Why it matters: Many attacks begin with stolen credentials that appear valid. Behavioral monitoring is often the only way to distinguish legitimate use from misuse, and it’s a core component of broader cyber resilience.
Auditors look for: Defined monitoring systems, clear escalation paths for alerts, and records showing how anomalies were investigated and resolved.
Best practice: Feed PAM activity data into SIEM platforms to flag suspicious patterns, and run tabletop exercises to validate detection and response. Apono’s cloud-native platform integrates privileged activity into security monitoring pipelines, giving teams faster visibility into high-risk behavior.
9. Vendor and Third-Party Access Controls
Vendors and contractors often need privileged access but don’t always receive the same level of oversight as internal staff. PAM audits examine how third-party accounts are provisioned, monitored, and retired.
Why it matters: Compromised vendor accounts can become the most straightforward path into critical systems.
Auditors look for: Defined onboarding and offboarding workflows, time-limited entitlements, and audit logs that cover external users as thoroughly as internal ones.
Best practice: Grant vendors just-in-time access with narrowly scoped privileges and automatic expiration. Incorporating offensive cybersecurity techniques into your testing program ensures these third-party controls are validated continuously, not just at audit time.
Table 1: Summary of PAM Audit Components
| Component | Why it Matters | Auditors Look For | Best Practice |
| Comprehensive Inventory of Privileged Accounts | Forgotten or orphaned accounts are common attack targets. | Dynamic inventory continuously updated, not static spreadsheets. | Automate discovery & classification; assign lifecycle owners; use cloud-native discovery. |
| Verification of Least Privilege Enforcement | Standing privileges remain risky even when accounts are idle. | Proof that access is temporary, scoped, and revoked automatically. | Replace static admin groups with time-limited roles; monitor exceptions; use JEP for machine identities. |
| Access Request and Approval Workflows | Ad hoc approvals create gaps in accountability. | Clear request trails showing requester, approver, and reason. | Integrate workflows into Slack, Teams, or CLI with auditable trails. |
| Session Monitoring and Logging | Without detailed logs, forensic evidence and accountability are lost. | Tamper-resistant logs tied to identities and centralized for review. | Route logs into SIEM/SOAR; perform spot checks for accuracy. |
| Automated Access Expiration and Revocation | Dormant accounts are a common attack vector. | Expiration policies for human and machine identities with automatic revocation. | Use automated, time-bound policies; schedule periodic reviews. |
| Break-Glass and On-Call Access Mechanisms | Emergency access can bypass security without proper controls. | Documented policies, detailed logs, and retroactive justifications. | Define emergency roles with scoped privileges; require justification; enforce auto-expiration. |
| Compliance Alignment and Reporting | Clear proof of privileged access governance is required for regulators, customers, and partners. | Reports mapping controls to compliance clauses with supporting evidence. | Automate continuous compliance reporting to stay audit-ready. |
| Continuous Monitoring for Anomalous Behavior | Behavioral monitoring is often the only way to detect credential misuse. | Defined monitoring systems, escalation paths, and investigation records. | Integrate PAM data into SIEM; run tabletop exercises; use anomaly detection. |
| Vendor and Third-Party Access Controls | Compromised vendor accounts are a major entry point for attackers. | Onboarding/offboarding workflows, time-limited entitlements, and full audit logs. | Grant JIT access with scoped privileges; enforce MFA; log all vendor activity. |
Closing the Gaps with Just-in-Time Access
Privileged access has always been highly risky, and the rise in credential theft shows that traditional controls are not enough. A PAM audit helps uncover weak points before they’re exploited, but audits alone don’t close the gaps.
Apono steps in to automate JIT access, eliminating standing permissions that attackers often abuse. Auto-expiring privileges ensure access is revoked as soon as it’s no longer needed. Plus, engineers can request access in Slack, Teams, or CLI with every step logged. In emergencies, Apono’s break-glass and on-call flows give immediate access but still record detailed logs of who accessed what and when. Book an Apono demo and explore how automated PAM audits save time and reduce risk.