Extending Access Duration Without Breaking Flow

Gabriel Avner
February 9, 2026

Today we’re introducing Extending Access Duration, a new capability designed to solve a problem we kept hearing about from customers who rely on short-lived, approved access to sensitive systems.
Just-in-Time access is the right model for protecting critical resources. But real work does not always fit neatly into the time window defined when an access flow was created. When access expires at the wrong moment, it interrupts work, frustrates engineers, and often creates unnecessary operational overhead for security teams.
Extending Access Duration is about closing that gap without weakening security controls.
When Security Controls Bump Up Against Operational Needs
In speaking with engineering leads, most of the friction we heard about had nothing to do with teams questioning the need for time-bound access. It came from what happens when approved work takes longer than expected.
This shows up most often during:
- Debugging production issues
- Troubleshooting incidents
- Working on sensitive systems protected by short access windows
In these situations, access can expire mid-task. This means that:
- Sessions drop
- Scripts stop running
- Engineers lose context, and sometimes work
The only option is usually to request access again, which often means waiting for another manual approval.
That delay does more than slow people down. It creates pressure to ask for broader access up front, just to avoid getting blocked later. Over time, that undermines the very controls Just-in-Time access was meant to enforce.
Built for Real Work, Not Perfect Timelines
Extending Access Duration recognizes a simple reality: sensitive work rarely finishes exactly on schedule.
We’re giving teams a way to extend existing access grants, without widening permissions or weakening controls. Extensions are policy-driven, auditable, and fully configurable, keeping Just-in-Time access intact while making it usable in practice.
Extending Access Duration allows users to extend the revocation time of an existing access grant instead of starting over with a new request.
The distinction matters. This is not a new access request, and it does not expand scope or privileges. It simply extends the duration of access that was already approved, under conditions defined by security.
From the user’s perspective, the experience is intentionally simple. When access is about to expire, they receive a notification. With a single click, they can extend the session and keep working without interruption.
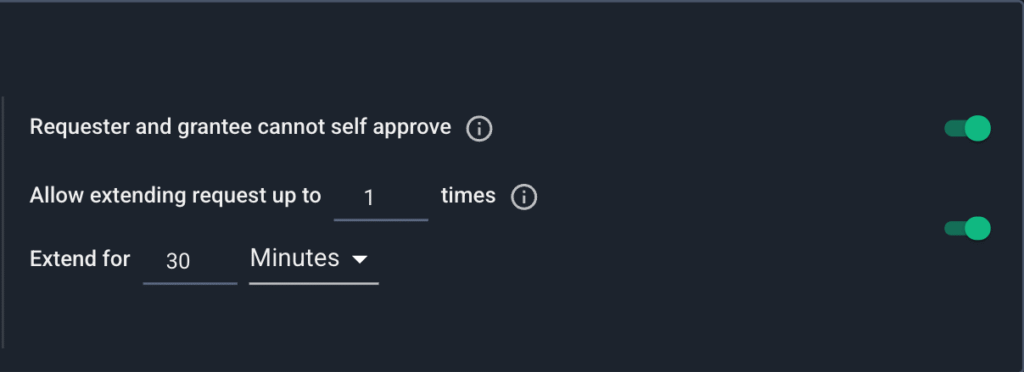
Admins can define exactly how long access can be extended, and how many times, directly within each Access Flow policy, keeping control simple, explicit, and consistent.
There is no reauthentication, no session teardown, and no credential rotation. The work continues as expected.
Security Controls Stay in Place
The Extending Access Duration capability is fully governed by admins and configured per access flow. Security teams decide:
- Whether an access flow is eligible for extension
- How long an extension can last
- How many times access can be extended
These controls are granular and policy-driven. Teams can enable extension where it makes sense and keep stricter rules where it does not.
All existing guardrails remain intact.
- Segregation of duties still applies.
- Users cannot approve their own access.
- Every extension event is logged and auditable, including when it happened and by how much access was extended.
This preserves the integrity of Just-in-Time access while removing unnecessary friction.
Breaking Down the Impact for Stakeholders
Extending Access Duration helps align access controls with how work actually happens.
- For engineers — Finishing the task they are already working on without getting kicked out at the worst moment.
- For security teams — Reduces approval churn, limits incentives to overprovision access, and keeps policies enforceable without becoming blockers.
- For admins — Lowers operational noise while maintaining clear oversight and auditability.
Most importantly, it allows teams to maintain strong access discipline without sacrificing productivity when reality runs longer than expected.
Why This Matters
Our Extending Access Duration is not about relaxing security. It is about making Just-in-Time access resilient to real-world conditions.
Sensitive access still expires. Approvals still matter. Privileges remain scoped and temporary. What changes is that teams no longer have to choose between staying secure and staying productive when a task takes a little longer than planned.
That balance is exactly what modern access management should deliver.
Make Just-in-Time Access Work in the Real World
Extending Access Duration is part of Apono’s broader approach to policy-driven, least-privilege access that adapts to real operational conditions. Security stays intact. Productivity stays uninterrupted.
Book a demo to see how Apono balances control, auditability, and engineering velocity.