Passing SOC 2 Without the Overhead: How Zero Standing Privileges Simplifies Compliance

Gabriel Avner
February 4, 2026
Getting ready for a SOC 2 audit can feel like an endless checklist. You already have tools collecting logs, provisioning users, and pulling reports from your systems, yet proving compliance still feels harder than it should be.
The biggest pain in SOC 2 is not collecting data. It is managing access in a way that continuously aligns with your own policies. A quick audit readiness assessment often reveals gaps teams don’t see day-to-day—standing access that was never removed, permissions that are broader than necessary, or controls that exist on paper but aren’t consistently enforced. You can have all the right information, but if your access privileges are stale, inconsistent, or overly broad, you are already behind.
Why SOC 2 Audits Still Hurt
Most organizations do not have a collection problem. They have a management problem.
The challenge is not getting the data. It is turning that data into consistent, enforceable access control across all your systems.
If identities are overprivileged, access policies have not been updated in months, or users have standing access to sensitive resources they rarely use, you are out of step with SOC 2 requirements before the audit even starts.
Then comes the harder question: how do you prove to auditors that least privilege is being enforced, not just once, but continuously?
How do you maintain least privilege after the cleanup is done and access starts drifting again?
If you can create, manage, and enforce your access policies centrally, you can get ahead of the pain by preventing access risks from becoming violations in the first place.
Zero Standing Privileges: Compliance That Enforces Itself
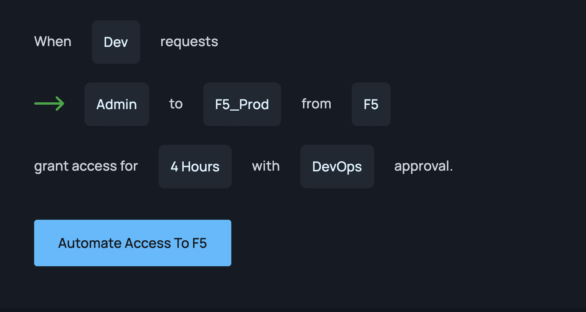
Zero Standing Privileges, ZSP, is a simple but powerful idea. Instead of granting users or service accounts ongoing access, ZSP removes always-on privileges and replaces them with access that is temporary, scoped, and granted only when needed.
With ZSP, access is:
- Purpose-based
- Time-bound
- Automatically revoked
This approach directly supports SOC 2 requirements for restricting access (CC6.1), enforcing least privilege (CC6.2), and revoking access promptly when it is no longer needed (CC6.3). It also aligns with the broader expectations in CC3.2 and CC3.3 for ongoing risk management and oversight.
ZSP simplifies compliance by reducing your attack surface and minimizing your blast radius.
More importantly, it creates an environment where least privilege is easier to maintain and easier to prove.
Instead of retroactively showing that privileges were reviewed and removed, ZSP makes unnecessary access impossible by design.
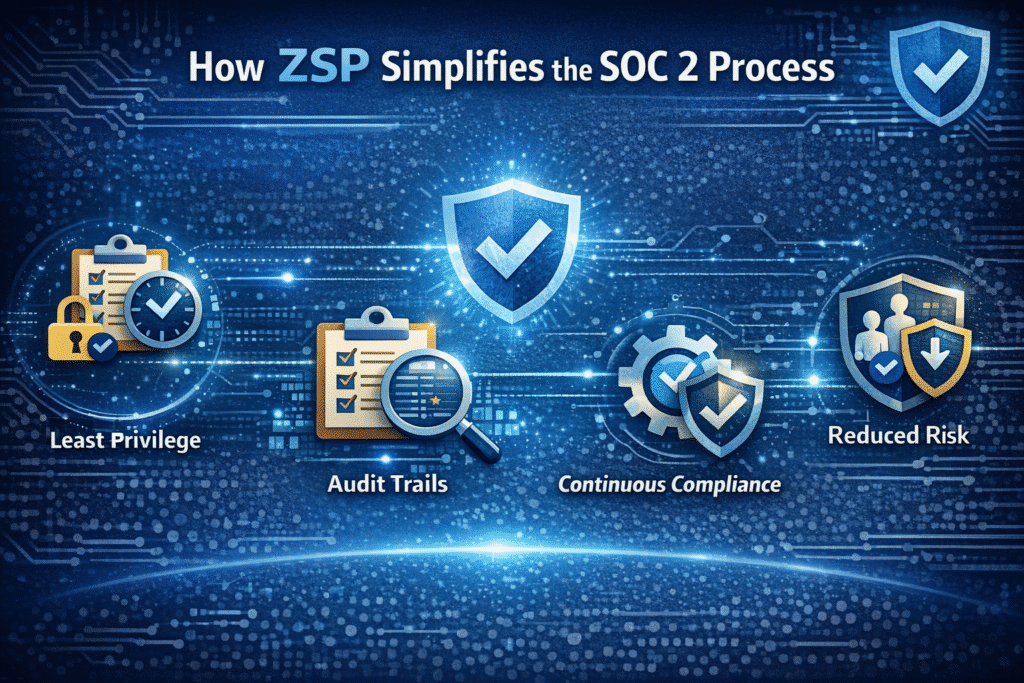
How ZSP Simplifies the SOC 2 Process
When ZSP is part of your access model, several SOC 2 challenges become far more manageable.
- Least privilege is built in
Because access is temporary and tied to specific tasks, you no longer depend on manual reviews to fix privilege drift. You can show auditors that access is granted only when needed and removed automatically. - Evidence comes automatically
ZSP naturally produces a complete audit trail. Every access request, approval, and revocation is logged in real time. This reduces the need for screenshots, spreadsheets, or stitched-together reports from different systems. - Compliance becomes ongoing
With ZSP, access controls operate continuously. You do not need to scramble before audits because least privilege is enforced operationally, not manually. - Risk is systematically reduced
Removing standing access lowers the chance of exposure across humans, service accounts, and AI agents, which reduces both security risk and compliance risk.
ZSP turns SOC 2 from a reactive process into an operational standard.
Turning ZSP into Reality with Apono
ZSP is a strong foundation, but it can be difficult to implement without the right automation and visibility. Apono makes it practical.
Apono gives security teams a unified access policy engine that allows them to implement, enforce, and monitor ZSP across their cloud and hybrid environments.
Dynamic, ephemeral roles
Apono creates temporary, context-based roles on demand. Access is granted Just-in-Time, scoped Just-Enough, and expires automatically.
Continuous monitoring and logging
Every access action, from request to approval to revocation, is logged with full detail. This produces audit-ready evidence that aligns with SOC 2, ISO 27001, HIPAA, and other frameworks.
Automated access reviews
Apono simplifies user access reviews by giving managers clear insights into who had access, why they received it, and whether they used it. This turns periodic certifications into quick, accurate decisions.
Right-sized privileges
Apono continuously evaluates privilege usage and risk. Overprivilege is flagged and remediated, which helps maintain least privilege across human, machine, and AI identities.
Unified policy engine
Apono applies consistent access policies across AWS, Azure, GCP, Okta, Entra ID, and more. Instead of managing fragmented access across dozens of tools, you define and enforce policy in one place.
Making SOC 2 a Seamless Process
When you automate access control with Apono and enforce Zero Standing Privileges, compliance becomes part of your operating rhythm. Least privilege is maintained continuously, audit evidence is always available, and access risk is significantly reduced.
SOC 2 stops being something you prepare for once a year and becomes something your systems uphold every day.
With the combination of ZSP and Apono’s automation, organizations can streamline compliance for SOC 2, ISO 27001, HIPAA, and other regulatory frameworks without adding overhead or slowing productivity.
Next Step
When access controls are enforced continuously, SOC 2 stops being a once-a-year scramble and becomes part of how your systems operate every day.
To understand where your current access model may still introduce audit friction, it helps to start with a simple self-assessment. The Audit Readiness Checklist lets teams evaluate access visibility, least privilege enforcement, Just-in-Time controls, and evidence generation so gaps are identified early, not during the audit.
From there, you can explore how Zero Standing Privileges and automation reduce that overhead altogether.
Our SOC 2 Compliance Datasheet also explains how continuous access enforcement supports ongoing, verifiable compliance without slowing teams down.