Top 7 Secret Scanning Tools for 2026

The Apono Team
December 24, 2025

Secrets run your applications: API keys, SSH keys, tokens, passwords, database credentials. They reside in repositories, CI/CD pipelines, infrastructure-as-code templates, containers, and even chat logs; one stray commit is enough to expose a path into production.
In 2024, abuse of valid account credentials was the initial access vector in roughly 30% of incidents investigated. At the same time, machine identities now outnumber humans by more than 80 to 1, many of which are tied to long-lived secrets that are difficult to manage.
Secret scanning tools help you stay ahead of this by automatically searching code and configuration for exposed credentials across GitHub, GitLab, CI/CD pipelines, and cloud resources so you can revoke and rotate them before an attacker simply logs in.
What are secret scanning tools?
Secret scanning tools are automated security solutions that detect exposed credentials, such as API keys, tokens, passwords, and connection strings, before they can be abused, and provide the necessary information to remediate them quickly. They continuously analyze sources like code repositories, configuration files, IaC templates, container images, and logs to catch secrets that end up in places they shouldn’t. Hence, scanning complements your broader secrets management strategy.
Most tools integrate directly with GitHub and other version control and CI/CD systems. Some run as static scans against code and configuration at rest, while others operate dynamically in pipelines, runtimes, and cloud environments to catch drift and secrets that surface only at execution time.
Even the best scanners only detect exposed credentials; they can’t fix the root causes behind secret sprawl: standing privileges and unmanaged non-human identities (NHIs). Scanning can surface these leaks, but it cannot right-size permissions or prevent overprivileged service accounts from becoming high-value breach targets.
Pairing secret scanning with Just-in-Time (JIT) access and least-privilege policies ensures that even if a secret leaks, its underlying permissions are time-bound and far less dangerous.
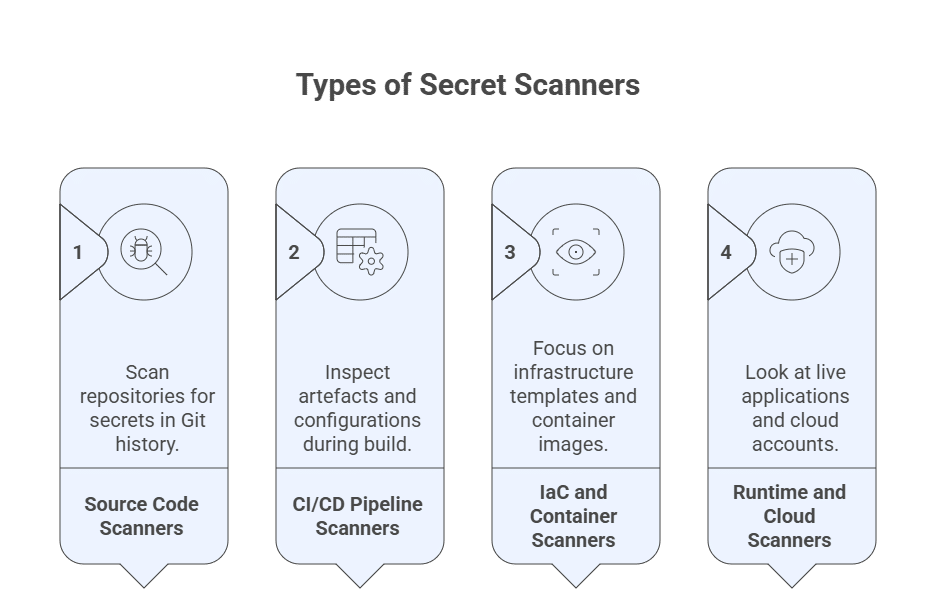
Types of Secret Scanning Tools
Secret scanning shows up at different layers of the delivery pipeline. In practice, most teams combine several types of tools to cover source code, build processes, and infra.
- Source code scanners run against repositories to detect secrets committed to the Git history or stored in branches and pull requests. They typically plug into GitHub, GitLab, or Azure Repos and surface findings directly within the developer workflow.
- CI/CD pipeline scanners run as part of build and deployment pipelines. They inspect artefacts, environment variables, and config files generated at build time.
- IaC and container scanners focus on infrastructure-as-code templates and container images, including configurations used in cloud or on-prem data center management environments.
- Runtime and cloud environment scanners look at live applications and cloud accounts. They detect secrets left in logs, storage buckets, or configuration stores that only appear after the system is live.
Benefits of Secret Scanning Tools
- Stronger security posture: Centralizes how you check secrets across code, pipelines, infrastructure, and cloud.
- Faster incident response: When a key leaks, you can quickly see where it “lives”, who uses it, and what to rotate.
- Better developer productivity: Checks in Git and CI/CD reduce security tickets and late rework by keeping feedback inside dev tools.
- Easier Compliance: Provides evidence that you monitor exposed credentials and enforce access-key policies, which simplifies SOC 2, ISO 27001, PCI and similar compliance regulations.
- Protection for non-human identities (NHIs): Reduces the chance that powerful service accounts and workloads are left with hard-coded, long-lived credentials. NHIs hold a high volume of operational privileges in most cloud environments, which is why teams increasingly rely on NHI management tools to understand and control how these identities use secrets.
Key Features to Look For in a Secret Scanning Tool
- Automated detection and remediation: Continuous scans in repos and pipelines that catch new secrets quickly and can open tickets or trigger revoke-and-rotate steps with your secrets manager, reducing the window in which exposed keys could be used in credential attacks.
- Context-aware, granular policies: Controls you can tune by repository, environment, secret type, and identity. This way, production or high-privilege secrets are handled differently from low-risk test data, following the principle of least privilege and time-bound access patterns.
- Seamless developer experience: Findings in pull requests or pre-commit hooks (with low noise and clear guidance) so teams adopt scanning without feeling blocked.
- Cloud-native, API-driven architecture: First-class support for multi-cloud, containers, and IaC, plus APIs and webhooks to feed results into internal platforms, chat, and automation.
- Centralized visibility and reporting: Dashboards and exports that highlight unresolved high-risk secrets and coverage gaps over time for security and GRC teams, a key requirement for root-cause analysis.
Top 7 Secret Scanner Tools
1. GitGuardian

GitGuardian is a dedicated secrets security platform that scans code repositories, CI/CD pipelines, infrastructure-as-code, and developer tools for hard-coded credentials and other sensitive tokens. It centralizes incidents and secret inventory across GitHub, GitLab, Bitbucket, Azure DevOps, and more, with policy controls and workflows for triage and remediation.
Best for: Perimeter-wide secrets detection.
Price: Free tier for up to 25 developers. Business and Enterprise plans for larger teams.
Review: “I like GitGuardian best for its real-time detection of secrets in both public and private repositories and its easy integration with developer tools…”
2. Apono
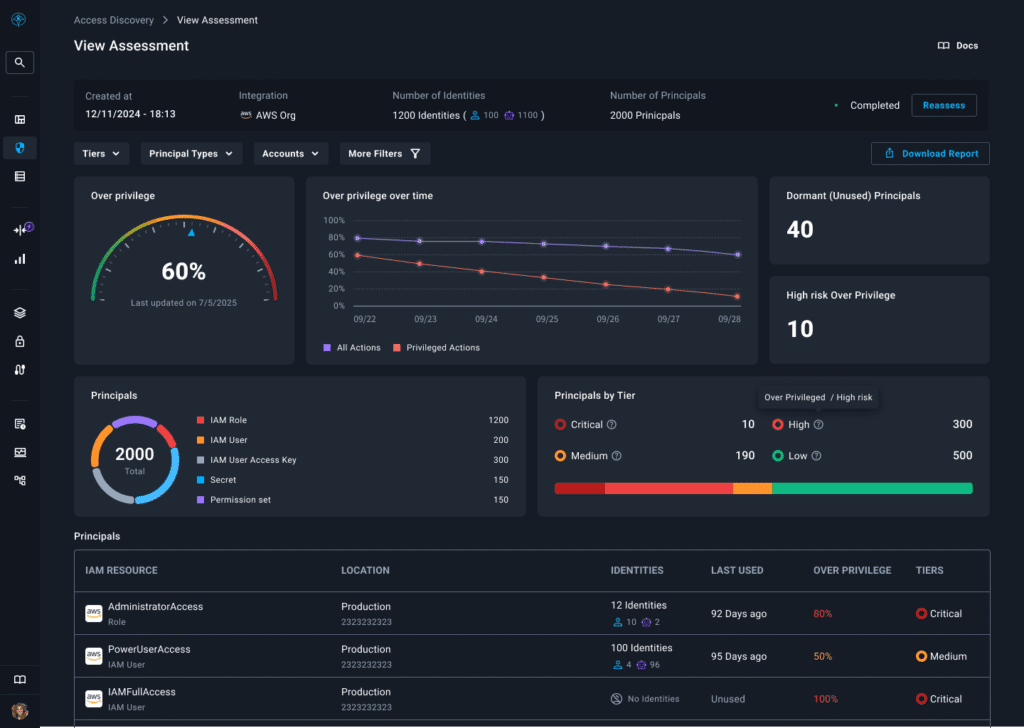
Apono is a cloud-native access management platform that eliminates the root causes of secret sprawl: standing privileges and unmanaged NHIs. Apono replaces standing privileges with JIT and Just Enough Privilege access to cloud and data resources for both human and machine identities. It connects to cloud platforms and identity providers to automate time-bound approvals and revoke-or-restore workflows, so credentials are only valid when needed.
Apono’s value becomes clear when combined with secret scanning: even if a credential leaks, its permissions are limited, temporary, and automatically revoked after use. Apono removes the need for long-lived IAM keys by brokering short-lived, scoped access through native cloud identity services.
Best for: Engineering teams that need automated, least-privilege access without slowing down developers or managing credentials manually.
Price: 30-day free trial with subscription pricing based on environments and usage.
Review: “Quick and easy config to integrate access control with a myriad of service providers and data stores.”
3. TruffleHog

TruffleHog is an open-source secrets scanning engine that digs through git history and other sources, such as local files, S3 buckets, Docker images, and logs, to find leaked credentials. It supports hundreds of secret types, utilizing both pattern- and entropy-based detection, and can validate many findings against provider APIs to reduce false positives.
Best for: Granular and extensive customization.
Price: Free and open source, with a paid enterprise edition available from Truffle Security.
Review: “Trufflehog offers a versatile solution for keeping your code’s secrets under wraps, available both as an open-source tool and as an enterprise solution.”
4. Yelp detect-secrets
Detect-secrets is Yelp’s open-source Python scanner that inspects a repository’s current state for high-entropy strings and known secret patterns, using a baseline file to manage existing findings. It’s lightweight enough for pre-commit hooks and CI/CD jobs, and extensible via plugins and custom rules when you need organization-specific detectors.
Best for: Low-overhead CLI scanning.
Price: Free and open source.
Review: “Detect-secrets by Yelp takes a minimalist approach to secret scanning, focusing on high accuracy and low operational overhead.”
5. Doppler
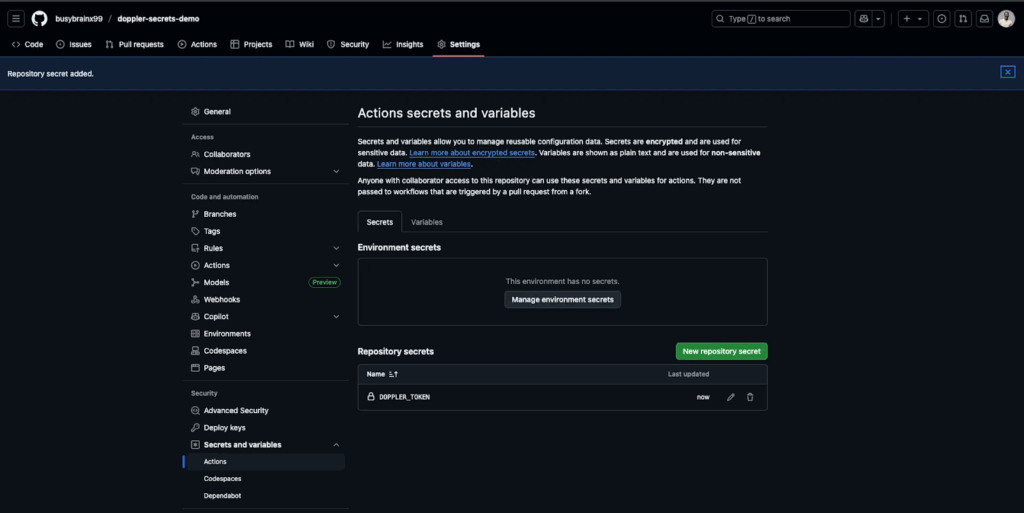
Doppler is a hosted secrets management platform that centralizes environment variables and API keys, then syncs them to apps, CI/CD pipelines, and cloud platforms as up-to-date configuration. It combines secret storage with basic scanning and auditing features, helping teams standardize how secrets are distributed and rotated while relying on dedicated scanners to find new leaks.
Best for: Managing a “source of truth” for secrets alongside separate secret scanning tools.
Price: Free Developer plan with paid plans with per-user pricing.
Review: “Doppler is one of those tools that I don’t want to imagine not having in my stack.”
6. Nightfall AI

Nightfall AI is an AI-native data loss prevention platform that also scans source code and git history for secrets via GitHub Actions, CI integrations, and DLP APIs. It detects credentials and API keys alongside PII/PHI in tools like GitHub, Slack, Google Drive, and other SaaS applications, allowing you to enforce consistent policies across repositories and cloud services.
Best for: Combining DLP and secret scanning across many apps and services.
Price: Free tier and paid volume-based pricing.
Review: “Nightfall is very easy and quick to rollout compared to a lot of other DLP products.”
7. AWS IAM Access Analyzer
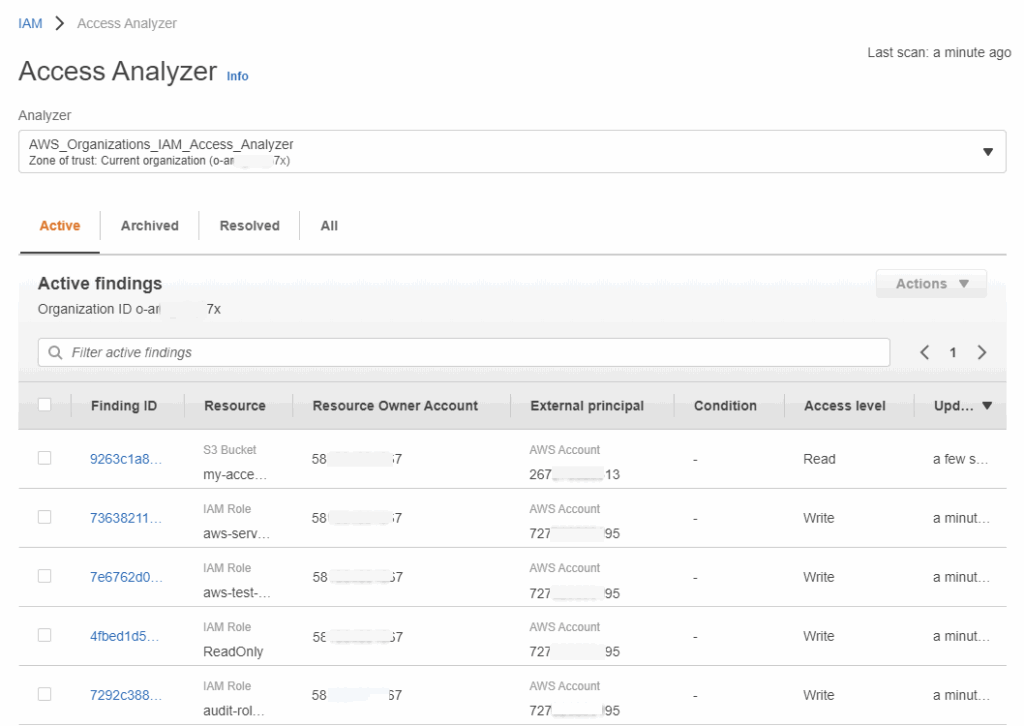
AWS IAM Access Analyzer is a native AWS service that analyzes IAM and resource-based policies to identify public and unused access to your AWS resources. It also validates and generates fine-grained policies based on access activity, encouraging least-privilege permissions and reducing blast radius if secrets or credentials are abused.
Best for: AWS-centric secret scanning.
Price: Billed per resource, identity, or API call.
Review: “The fact that it enables me to precisely regulate user access is what I value most.”
The Hidden Secrets of Secret Scanning
Secret scanning tools are now vital for teams shipping continuously. They provide visibility into exposed credentials across code, CI/CD pipelines, infrastructure, and cloud, allowing you to revoke and rotate them before an attacker gains access.
On their own, though, scanners are reactive. They can tell you a secret has leaked, but not what it can do, or how long it should stay valid. Controlling attack blast radius requires access policies that default to no access and grant short-lived, least-privilege permissions based on context, such as user, role, resource, and variables like time of day or location. This is the missing half of the equation; detection without automated, zero-standing privilege access controls still leaves your organization exposed.
This is where an access platform like Apono fits into the picture. Apono automates just-in-time, just-enough access for both human and machine identities across your cloud and data stack, so most credentials are short-lived and tightly scoped. It removes the operational overhead of manually granting or revoking access and eliminates long-lived keys across pipelines, tools, and workloads.
If you’re working to reduce secret sprawl and eliminate long-lived credentials, explore our PAM Buyer Guide for a deeper breakdown. Alternatively, book a personalized Apono walkthrough to see how automated JIT access closes the gaps secret scanning tools can’t.



![The Required API Security Checklist [XLS download] post thumbnail](https://www.apono.io/wp-content/uploads/fly-images/20485/The-Required-API-Security-Checklist-600x312.png)


