Why Entra ID Privileged Identity Management Breaks Down in Multi-Cloud Audits

Gabriel Avner
April 7, 2026
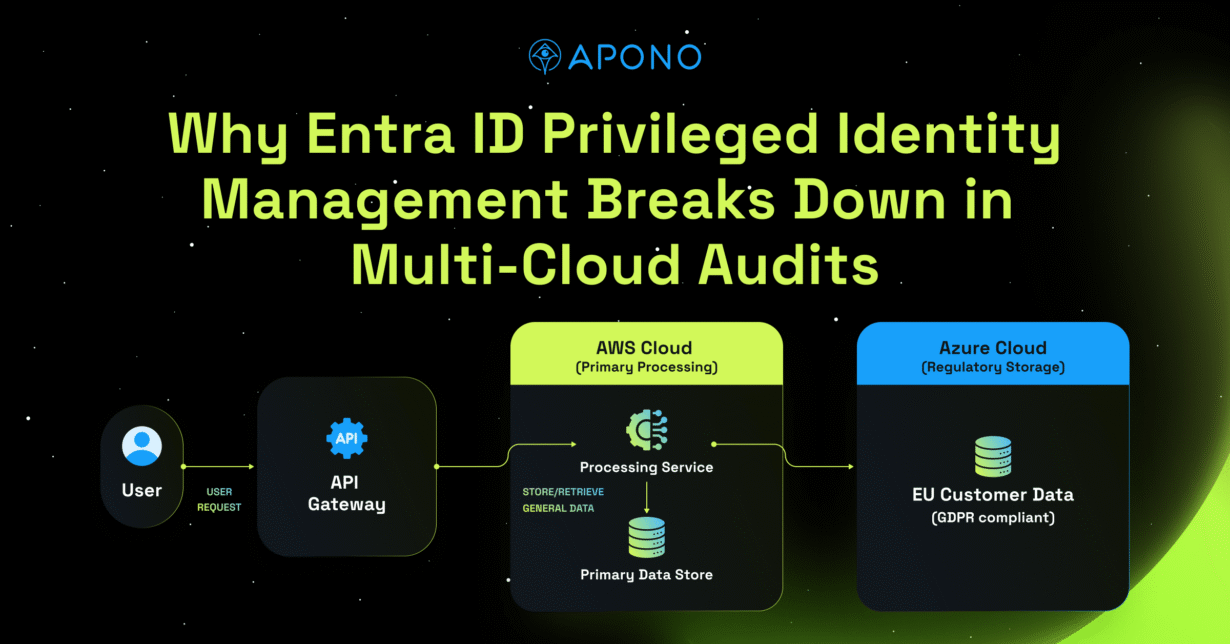
For many enterprise security teams, audit season feels less like validation and more like reconstruction. Not because they lack logs, and not because their teams are careless, but because their privilege model was never designed to produce a clean, unified story. In Microsoft Entra ID environments, Privileged Identity Management (PIM), works well as long as your world is entirely Microsoft.
But no enterprise operates in a single-vendor bubble.
The moment your infrastructure spans Azure, AWS, Kubernetes, databases, SaaS platforms, and/or hybrid systems, auditing privileged access becomes fragmented. What was once a straightforward activation workflow turns into a cross-system investigation exercise.
| Asset Type | Tooling Required |
| Azure | Entra ID PIM |
| AWS | AWS IAM + Identity Center |
| GCP | Google Cloud IAM + PAM |
| Kubernetes | RBAC + manual namespace policies |
| Databases | Native DB permissions + manual access controls |
| SaaS platforms | Per-app admin consoles (Salesforce, Okta, GitHub, etc.) |
| Hybrid / on-prem | Active Directory + Legacy PAM |
That is not a configuration issue, it’s a control model issue.
Where the Friction Actually Shows Up
Inside Entra, PIM can require approval, time-bound role, and log activation. Within Azure, that can be enough to show that elevation occurred.
But auditors for SOC 2, ISO 27001, and other compliance frameworks do not ask whether elevation occurred. They ask broader questions. Who had privileged access to production? Under which approval? For how long? What actions did they take? Was this enforced consistently across environments?
The moment those questions extend beyond Azure, the resources needed to get answers start to scatter.
Security teams export PIM activation logs, correlate Azure activity logs, gather AWS CloudTrail, review Kubernetes audit logs, and cross-reference ITSM tickets. Then they manually stitch together timelines to approximate a complete picture.
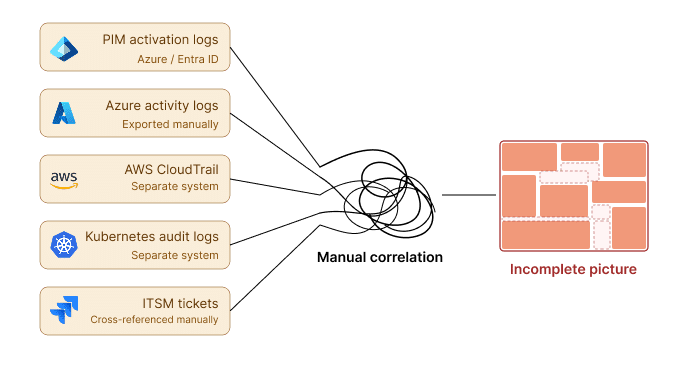
Even then, these disparate systems paint an incomplete picture. Auditors need to know specific details like:
- Who had privileged access to production?
- Under which approval?
- For how long?
- What actions did they take?
- Was this enforced consistently across environments?
Activation logs show that someone elevated, but they don’t tell the story of how privilege was governed and exercised across systems.
That gap is where audit preparation becomes slow, manual, and unnecessarily stressful.
PIM’s Scope is too Narrow for Enterprise Architectures
This is not about dismissing PIM. It solves a specific problem (i.e. temporary elevation inside Microsoft’s ecosystem), but enterprise privileged access governance is much broader.
The limits of PIM’s functionality leaves several gaps that compliance teams must find other ways to account for:
- PIM does not eliminate standing privilege across all environments
- It does not provide unified lifecycle visibility across cloud platforms
- It does not standardize approvals outside Microsoft systems
- It does not connect privileged actions back to approvals in a structured, cross-environment way
So while elevation inside Azure may be controlled, the broader enterprise story remains fragmented.
And fragmentation is what makes audits painful.
An auditor is not looking for five different log sources. They want one coherent explanation of who did what, when, and why, along with evidence that the process is consistent everywhere.
If assembling that explanation requires correlating multiple systems that were never designed to operate as one, the burden lands on security and identity teams – which only increases as environments scale.
Today, humans elevate across clouds and platforms. And as automation and AI-driven workflows proliferate, they will operate across those same systems at speed and volume that manual audit reconstruction cannot sustain.
If auditing is difficult now, it becomes unmanageable without rethinking the control model.
The Shift: Centralize the Control Model
Most teams try to solve this by improving reporting. They extend log retention, add dashboards, and invest in aggregation, hoping better visibility will ease audit friction.
That helps at the margins, but it does not fix the core issue. You are still correlating disconnected systems after the fact, stitching together logs that were never designed to tell one coherent story.
What actually changes the experience is centralizing privilege governance. When access is requested, approved, provisioned, and monitored through a single control layer, the audit narrative assembles itself. Evidence stops being something you scramble to collect during audit season and becomes something your control model produces continuously.
In practical terms, this means creating consistent guardrails across environments. Access is requested in a standardized way. Approval workflows are enforced consistently. Privileges are provisioned dynamically on the target system. Access expires automatically. Privileged activity is traceable from request through execution.
If these processes are not monitored and managed continuously then they will quickly become irrelevant as the cloud environments constantly and rapidly change.
When the control model is centralized and continuously monitoring, audit preparation becomes reporting instead of investigation.
How Apono Simplifies Audit Life
Apono was built as a centralized privilege control plane for multi-cloud and hybrid environments.
Identity providers like Entra ID and Okta continue to handle authentication, while Apono governs the privilege layer across cloud platforms, Kubernetes, databases, infrastructure, and SaaS systems.
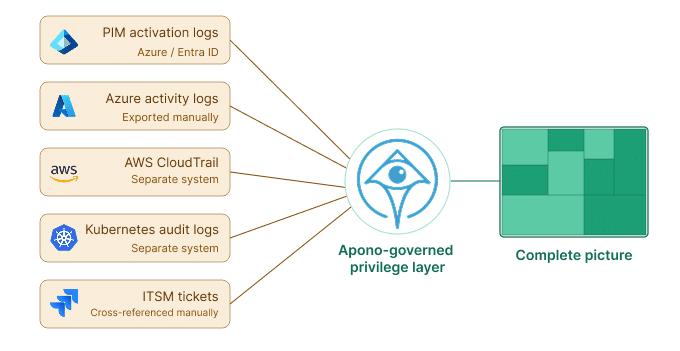
Instead of relying on standing access and scattered controls, Apono enables organizations to move toward Zero Standing Privileges by converting persistent permissions into time-bound, requestable access flows. It continuously surfaces and reduces unnecessary privilege across environments.
The impact becomes most visible during audits.
Because Apono manages the full access lifecycle – from request, to approval and provisioning, and all the way through to expiration – it becomes the source of truth for privileged access across systems.
With structured session auditing, it extends beyond provisioning events to capture the actions performed during access. Instead of replaying sessions or combing through and manually correlating raw logs, security teams can directly answer who accessed what, under which approval, for how long, and what actions occurred.
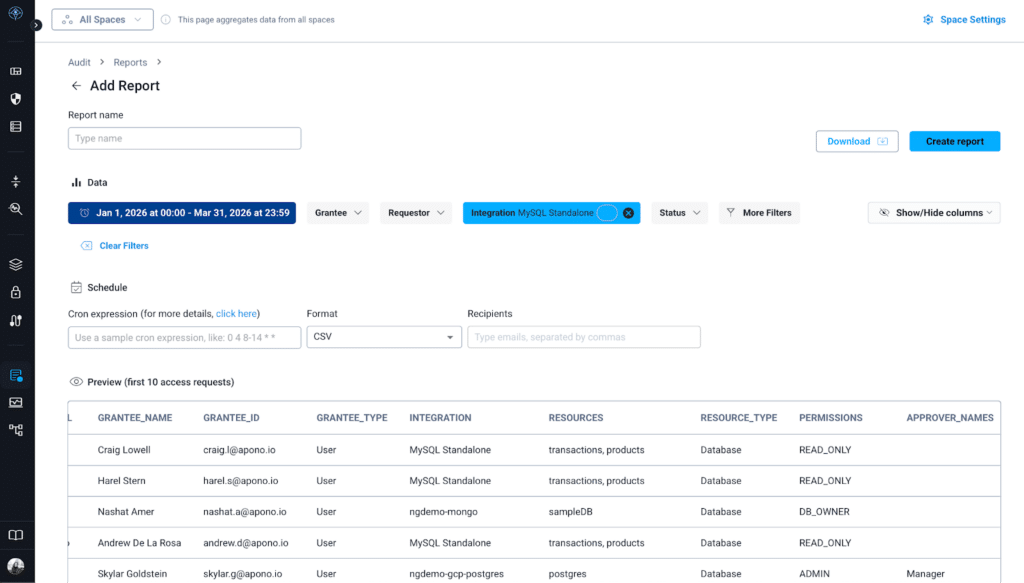
By centralizing privilege guardrails and connecting approvals to actions, Apono dramatically reduces the operational load of proving control.
With Apono, not only do audit preparation time drop and investigation time shrink, but conversations with auditors become simpler and more defensible.
A Different World Than PIM Was Built For
PIM was built for a Microsoft-centric world and enterprises do not operate in one.
As long as privileged access is governed in silos, audits will require correlation, manual effort, and reconstruction. The only scalable way to reduce that friction and prepare for the wide-scale deployment of agents across systems is to centralize the control model across environments and eliminate standing access by design.
When the control model changes, the audit experience changes with it.
Make Privileged Access Audits Simpler
In multi-cloud environments, proving who had privileged access and why often requires stitching together logs from multiple systems.
When access governance is fragmented, audit preparation turns into manual investigation.
A centralized privilege control model changes that. Access requests, approvals, and activity become traceable across environments, making audit evidence easier to produce and defend.
Evaluate your privilege model in a personalized session with our team.
Prefer to start on your own? Download the Audit Readiness Checklist to assess your environment.





![The Required API Security Checklist [XLS download] post thumbnail](https://www.apono.io/wp-content/uploads/fly-images/20485/The-Required-API-Security-Checklist-600x312.png)