7 Tips for Just-in-Time Privileged Access Management You Need to Implement Today

The Apono Team
December 4, 2025
Managing access can become tedious and clunky. Someone always ends up with too much power, someone else is locked out when something’s on fire, and no one remembers who approved what in the first place. It’s the slow creep of “we’ll fix it later.”
However, that “later” is catching up. A recent report found that 58% of security leaders expect the number of identities, human and non-human, to grow in the next year, adding even more strain to already fragile governance systems. In cloud-native environments, privileges tend to accumulate across AWS IAM roles and Kubernetes namespaces, creating persistent attack paths that are rarely audited.
Every new SaaS tool and automation job adds another credential that has to be tracked, rotated, and revoked. Most teams already struggle to stay ahead of what they have today, which is why it’s vital to implement Just-in-Time Privileged Access Management best practices.
What is Just-in-Time Privileged Access Management?
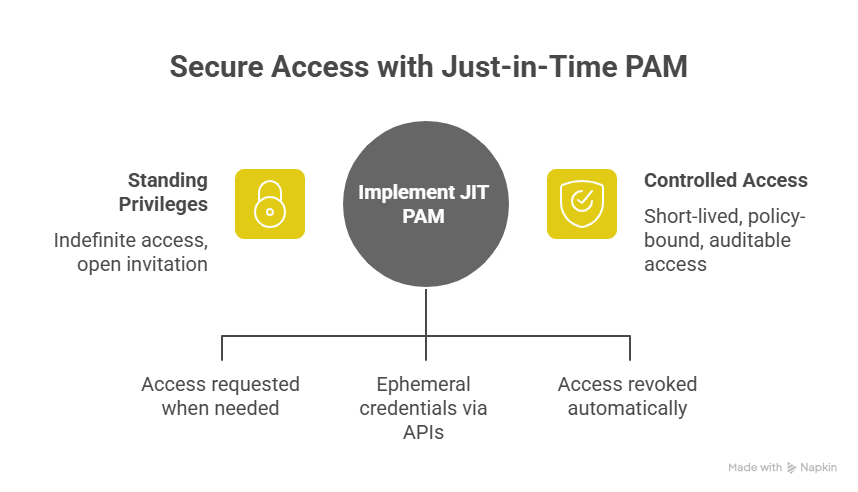
Just-in-Time Privileged Access Management (JIT PAM) exists to stop access drift. Instead of handing out standing privileges that last indefinitely, JIT PAM issues access only when it’s requested, for exactly as long as the policy allows, and then tears it back down automatically. JIT PAM uses ephemeral credentials issued via APIs or federated IAM roles. Access is time-scoped and automatically revoked through policy triggers once a task or session ends.
Essentially, it’s access that behaves more like an API call than a set of keys: granted for a purpose, then revoked once it’s served that purpose. Traditional PAM tools rely on vaults and rotation schedules, but the underlying permissions stay constant. JIT PAM treats privilege as something that should expire by default.
This approach matters because the environment has shifted. Non-human identities now outnumber human ones by more than 80 to 1. Every service account, container, pipeline, and bot carries its own credentials, each capable of the same lateral movement a compromised user could make. JIT PAM brings those identities under the same control model as humans (short-lived, policy-bound, and fully auditable), so that “access” stops being an open invitation and starts being a controlled event.
Key Components of Just-in-Time PAM
The point of JIT PAM is to enforce intent by making sure that every action in the system is traceable and linked to a deliberate choice. In modern environments, these policies are often defined as code (IaC) and triggered automatically when a developer or service account requests access, ensuring consistent enforcement across environments.
1. Automated Policy-Based Provisioning
Every credential has a lifespan. Nothing stays open longer than it should. When a session ends, the access that enabled it disappears, too. That single constraint changes how systems age, with fewer forgotten roles, fewer dormant tokens, and fewer cracks for attackers to find later.
2. Time-Bound, Auto-Expiring Permissions
Every privilege should have a defined lifespan. Access begins when the task starts and automatically expires once it’s complete; no manual cleanup or forgotten admin accounts lingering in the background.
By ensuring that every permission has a clear endpoint, you maintain a smaller and more predictable attack surface. Each access event leaves behind a complete audit trail that shows precisely when it was granted and when it ended. In a Just-in-Time PAM model, nothing persists longer than it needs to, by design.
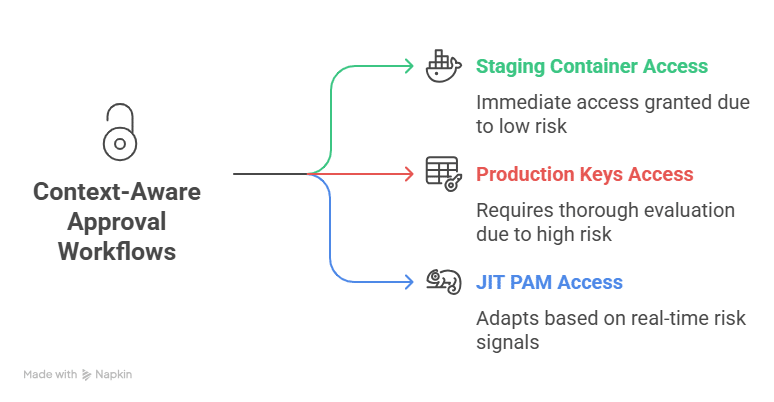
3. Context-Aware Approval Workflows
Access decisions are shaped by timing, intent, and the environment in which they happen. A developer spinning up a staging container might get in immediately. But someone requesting production keys is a different conversation.
JIT PAM reads signals such as identity, device trust, and resource sensitivity and adapts on the fly. It behaves less like a static rule set and more like a security reflex, adjusting itself to match the risk in front of it. Signals such as user behavior, device trust, and location are evaluated in real time to ensure access decisions match contextual risk. These workflows often assess contextual risk signals such as user identity, device posture, IP reputation, and real-time session behavior before granting access.
4. Comprehensive Audit Trails
A robust audit trail is an account of what actually happened. Every request, approval, and expiry automatically builds that record. Over time, those logs provide valuable visibility.
Security teams can trace actions back to intent, reconstruct incidents, and close loops without guesswork. When questions arise, the evidence isn’t buried in tickets because it’s already structured and searchable.
7 Tips for Just-in-Time Privileged Access Management You Need to Implement Today
JIT PAM is not something you install and walk away from. It is a continuous practice of auditing and adjusting access based on how people and machines actually work. The following best practices form the foundation of any strong JIT PAM implementation.
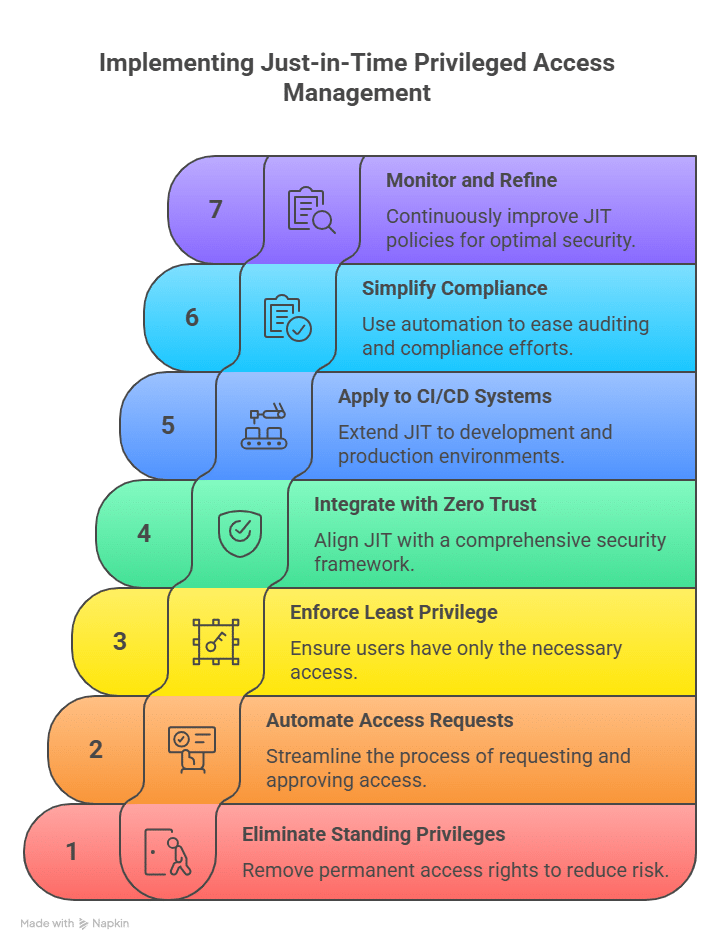
1. Identify and Eliminate Standing Privileges
Start with a full privilege audit. Automated discovery tools and policy-based permission expiry make this process repeatable and maintainable. Every environment accumulates what most teams call “zombie access,” such as credentials, tokens, and admin roles that were meant to be temporary. They stay in place long after they are needed, waiting to be exploited.
Conduct a full audit across human and non-human accounts to identify where standing privileges exist, then remove them in a structured way. Eliminating standing access reduces the number of open doors that attackers can use. Once identified, replace those static roles with time-bound, Just-in-Time (JIT) policies that automatically expire.
2. Automate Access Requests and Approvals
Manual access control slows down development and operations. Developers open tickets, wait for approvals, and eventually decide it is easier to keep elevated privileges “just in case.” That is how privilege creep begins.
Automating access requests fixes the root of the issue. Use cloud-native JIT PAM systems that integrate directly with your team’s existing tools, such as Slack, Microsoft Teams, or CLI. These integrations make it possible to grant temporary permissions dynamically based on context and policy. Access should feel simple to request and safe to revoke.
In a JIT PAM model, requests trigger API-based policy provisioning: when a developer requests access, an ephemeral credential or federated role is issued automatically, scoped precisely to the resource and duration defined by policy.
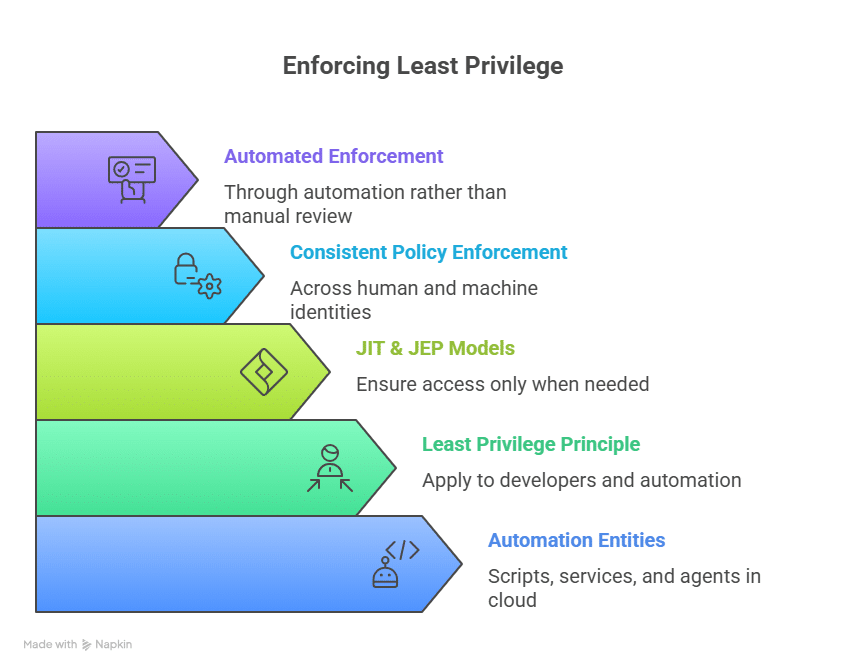
3. Enforce Least Privilege Across Human and Non-Human Identities
Cloud infrastructure is built around automation, meaning scripts, services, and agents, which now outnumber humans by a wide margin. Each entity holds potential access that can be compromised if left unmanaged.
The principle of least privilege should apply equally to developers and automation. JIT and Just Enough Privilege (JEP) models ensure that every identity, human or not, receives only the access needed for the specific task. This approach strengthens identity and access governance by ensuring consistent policy enforcement across human and machine identities. Apono extends this capability across workloads and service accounts, enforcing least privilege through automation rather than manual review.
4. Integrate JIT with Zero Trust Frameworks
JIT PAM and Zero Trust share the same goal: access is never assumed to be safe. Every request must be verified in context.
Access decisions become continuous and data-driven when JIT is applied within a Zero Trust architecture, much like how continuous penetration testing identifies and validates vulnerabilities in real time to ensure defenses adapt as environments evolve. Permissions are granted based on real-time conditions such as device posture, session history, and user activity. This approach ensures that even trusted users or systems are validated before every interaction. Cloud-native, policy-based controls make this achievable without creating extra work for the security team.
5. Apply JIT to CI/CD and Production Systems
Continuous integration and deployment pipelines often hide the most serious privilege issues. Tokens stay hardcoded in scripts, service accounts hold unnecessary admin roles, and access is shared to keep deployments moving quickly.
Applying JIT principles to your pipeline helps contain that risk. A cloud PAM approach extends these controls across CI/CD systems, ensuring credentials are issued only when needed and revoked automatically after use. You can choose a cloud-native access management platform that supports DevOps workflows by issuing temporary, scoped credentials for builds, deployments, and emergency access situations. Permissions exist only for the duration of the task and disappear when the work is done.
6. Simplify Compliance and Auditing with Automation
Every organization faces compliance checks, and most dread them. JIT PAM simplifies this by automatically logging every access event: who requested it, who approved it, and when it expired.
Automated logging makes compliance faster and more transparent, but visibility doesn’t end there. Many organizations also rely on external security oversight and continuous monitoring partners to strengthen their audit readiness and ensure alignment with frameworks like SOC 2, HIPAA, and GDPR.
7. Continuously Monitor and Refine JIT Policies
Access control changes as infrastructure and teams evolve. What is appropriate today can easily become excessive tomorrow.
Most teams don’t look at their own logs; they trust the policy and assume it’s working. However, it rarely is. Open the log data and you’ll see it immediately, such as access requests looping, temporary roles that never expire, and the same people asking for the same things. Regular reviews and automation are key DevSecOps best practices that ensure policies evolve as fast as your infrastructure does
Building Access Control That Works With You, Not Against You
Standing privileges are the silent failure point of modern security. They accumulate over time, stay invisible until something goes wrong, and create more risk than most teams realize. Just-in-Time Privileged Access Management changes that equation. It gives your organization a way to enforce least privilege, reduce exposure, and stay compliant without grinding daily operations to a halt.
Apono takes the heavy lifting out of that process. It deploys in under fifteen minutes and connects directly with the systems your teams already use, such as Slack, Microsoft Teams, and the command line. With Apono, permissions expire automatically once tasks are complete, ensuring least privilege by default. For urgent fixes, break-glass and on-call flows provide instant but controlled access that closes the loop once the incident is over.With Apono, you can see how automated, policy-driven access can replace manual approvals and standing admin roles. Request a demo today.





