Announcing Justification Coach: AI-Powered Guidance for Better Access Requests and Stronger Audits

Gabriel Avner
April 14, 2026
Today, we’re introducing Justification Coach, a new AI-powered capability that helps users write better access request justifications in real time, so admins get the context they need for audits and investigations without having to chase people down after the fact.
The Justification Problem No One Talks About
Every access governance platform asks users to justify their requests. It’s a cornerstone of compliance and a key input for auditors. In theory, it works great.
In practice? We keep hearing from customers that the justifications their teams are writing just aren’t cutting it.
Some are obviously junk:
- Random characters
- Whitespace
- Exclamation points
- Completely empty fields
Others are real words but barely more helpful, things like “access,” “working,” “dev,” or just a single abbreviation.
When we looked at the data, over 42% of justifications fell into one of these categories. And the rest weren’t necessarily much better, with many clocking in at just two or three words that still don’t communicate any real intent.
That matters because justifications serve two critical purposes.
- In a compliance audit, they’re how you demonstrate why someone had access to a sensitive resource. If an auditor asks “why was this person granted production access?” and the answer on record is “asdf,” that’s a problem you have to explain.
- During an incident investigation, justifications are supposed to help admins reconstruct what happened and why elevated access was granted. A one-word justification gives them nothing to work with.
Why Users Write Bad Justifications
It’s tempting to blame lazy users, but the reality is more nuanced.
Most access request forms give users a blank text box with no guidance on what a good justification looks like. There’s no feedback, no structure, and no indication of what “good” even means in that context.
So users do what people naturally do with unstructured fields under time pressure: they write the bare minimum and move on.
Some admins we spoke with told us they’ve resorted to manually rejecting requests with poor justifications, essentially playing a back-and-forth rejection game until the user provides something useful. That’s painful for everyone involved, and it doesn’t scale, especially when approver quality varies and not every approver is trained to enforce the same standard.
How Justification Coach Works
Instead of punishing bad justifications after the fact, we built a system that guides users toward better ones in the moment.
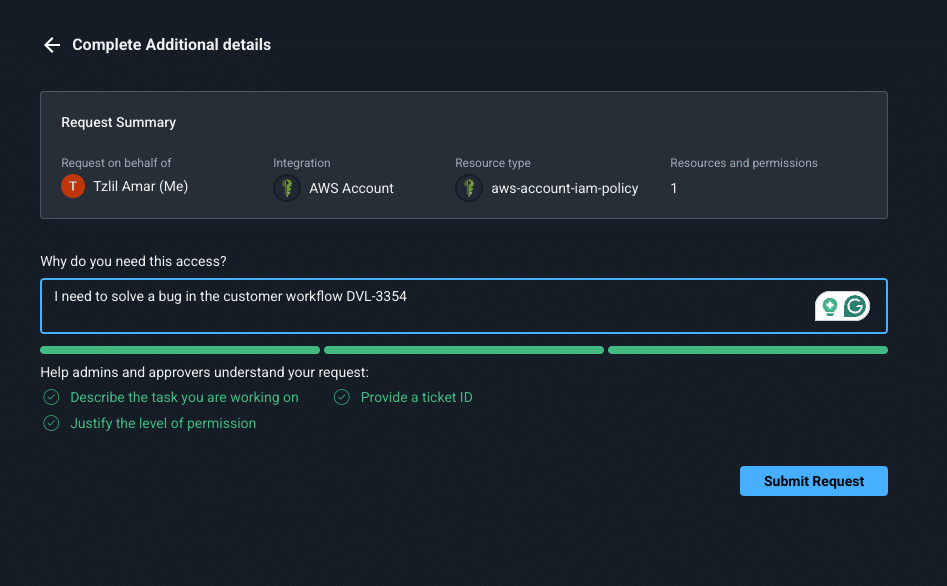
Think of it like the password strength meter you’ve seen on every signup form. As you type your justification, AI evaluates it in real time against a set of quality criteria and gives you visual feedback on how well your justification communicates your intent.
The validation looks at whether you’ve:
- Described your task so it’s clear what you’re actually trying to accomplish
- Justified the level of permission relative to what you’re requesting
- Included an action or verb that indicates specific intent
- Provided a reference like a ticket ID that ties the request to a trackable workflow
Because the AI also has context about the resource you’re requesting, the permission level you selected, and other metadata, it can make intelligent assessments.
If you’re requesting admin-level access but your justification only describes a read operation, the validation will flag that mismatch and nudge you toward a more precise request.
Enablement First, Enforcement later
One design decision we were deliberate about: in this initial release, Justification Coach is advisory, not blocking. Users see the feedback and quality indicators, but they can still submit their request even if the justification doesn’t hit every mark.
Why? Because we talked to customers and found something interesting.
Admins universally wanted this feature, but they also told us they preferred starting with enablement over enforcement. The goal right now is to teach users what a good justification looks like and build the habit organically, not to create a hard gate that adds friction without context.
That said, enforcement is on the roadmap. Customers have already asked for the ability to configure which access flows require a minimum justification quality, so admins will eventually be able to set that threshold per access flow based on sensitivity.
What’s Next: From Validation to Intent
This feature is part of a bigger story around how Apono understands user intent.
Right now, we’re setting up the guardrails that improve justification quality across the board. Over time, as that quality improves, the data opens up new possibilities:
- Smarter autocomplete based on context
- Pre-filled justifications based on similar past requests
- Deeper integration with ticketing systems to automatically pull context from linked issues
The vision is straightforward. The better Apono understands what a user is trying to do and why, the better it can streamline the entire access experience, from request to approval to audit, while keeping access scoped, time-bound, and fully documented.
See it in Action
Bad justifications aren’t just an annoyance. They’re a compliance gap and an investigation blind spot.
Justification Coach helps close that gap by guiding users toward meaningful justifications at the point of request, reducing admin overhead and producing audit-ready access records without any additional configuration.
Book a demo to see how Justification Coach can strengthen your access governance.