Vendor Acquired? What It Means for Your PAM Strategy

Gabriel Avner
January 22, 2026

Over the past two years, we’ve watched a steady wave of acquisitions reshape the privileged access market. For many security leaders, that wave has now hit home. Your PAM vendor has been acquired, absorbed into a larger platform, and suddenly the roadmap you once relied on feels less certain.
This moment is easy to dismiss as “business as usual.” It is also one of the rare points where it actually makes sense to step back and reassess your PAM strategy with fresh eyes.
Vendor acquisitions are not inherently bad. In many cases, they validate the importance of the problem being solved. But they also change incentives, priorities, and pace. For organizations that already feel friction around access management, cloud scale, or AI readiness, this can be a practical opportunity to decide whether staying put still makes sense, or whether it’s time to look at alternatives built for where access is headed next.
Why PAM Consolidation Is Accelerating
The recent acquisition activity reflects a growing recognition that identity, and particularly privileged access, has become foundational to security in the cloud and increasingly to AI-driven environments.
In the past two years alone, we’ve seen:
- 2024
- CyberArk acquires Venafi to expand coverage for non-human identities for $1.5 billion
- BeyondTrust acquires Entitle for roughly $150M
- 2025
- 2026
- CrowdStrike acquires SGNL for $740M
- Delinea acquires StrongDM for undisclosed amount
There are two clear signals here.
First, large security platforms understand that controlling privileged access is essential as organizations move toward AI-driven operations. They are buying capabilities to ensure they are not caught flat-footed, the way many were during the initial cloud transition.
Second, identity-focused vendors recognize that legacy PAM architectures built for on-prem environments are no longer sufficient. The shift to cloud infrastructure, API-driven services, and autonomous systems demands a different approach to access control.
For customers, however, these acquisitions raise an important question. Does the new parent company’s vision align with what you actually need from PAM going forward?
How Can an Acquisition Impact Your PAM Strategy Right Now?
When a startup is acquired by a large platform, the technology does not disappear overnight. But the dynamics around it often change.
Product direction may shift toward platform alignment rather than customer-driven innovation. Roadmaps slow as teams integrate codebases and processes. Support models change. Features that were once core can become secondary to broader platform goals.
This does not automatically make the solution worse. But it does change the calculus for customers who were relying on that vendor to solve specific access challenges at cloud scale.
More importantly, it creates a natural pause point. A chance to ask whether your current PAM approach is positioned to handle what comes next, not just what worked yesterday.
Identity, Cloud Scale, and Why Static Models Fell Behind
Privileged access management worked reasonably well in the on-prem era because the environment was stable.
Infrastructure changed infrequently. Permissions were coarse-grained. Identities were almost entirely human. Static roles and periodic access reviews, while inefficient, were manageable.
That world no longer exists.
The move to the cloud fundamentally changed the problem:
- Infrastructure adoption accelerated faster than most security programs anticipated
- Resources multiplied and permissions became increasingly granular
- Change shifted from quarterly to daily
Even when identity management was limited to humans, static roles and periodic reviews struggled to keep up.
Then came the explosion of non-human identities.
Service accounts, workload identities, API tokens, CI/CD pipelines, and automation are now embedded everywhere. These identities are predictable in function, but they exist at massive scale. Estimates now place the ratio of non-human identities to humans at roughly 150:1.
Most of these identities sit outside traditional IdPs like Okta or Entra ID. Visibility is fragmented. Lifecycle management is weak. Permissions are often left overly broad because teams are understandably afraid of breaking production workflows.
Now we are entering the Agentic AI era, where earlier cracks widen further.
AI agents combine human-like autonomy with machine speed and scale. They decide what to access, when to act, and how to proceed, often without direct human oversight. If non-human identities were already a scaling challenge, AI is a multiplier.
This is why identity has become the limiting factor for both cloud security and AI adoption.
Why “Modern PAM” Still Fell Short
Some newer PAM solutions attempted to address cloud access challenges, but many carried forward assumptions that no longer hold.
Tools like StrongDM and Teleport were built around proxies and local network concepts. They change how engineers connect, introduce operational overhead, and require agents and pre-created roles. That model can work in certain environments, but it still slows teams and shifts complexity onto admins.
Other tools, like Entitle, introduced API-based connectivity but continued to rely on static, pre-defined roles. That reduces some friction, but it does not eliminate role sprawl, privilege accumulation, or manual maintenance.
The common thread is static management. Roles are still defined ahead of time, permissions accumulate over time, and reviews happen after the fact.
That model struggles under continuous change.
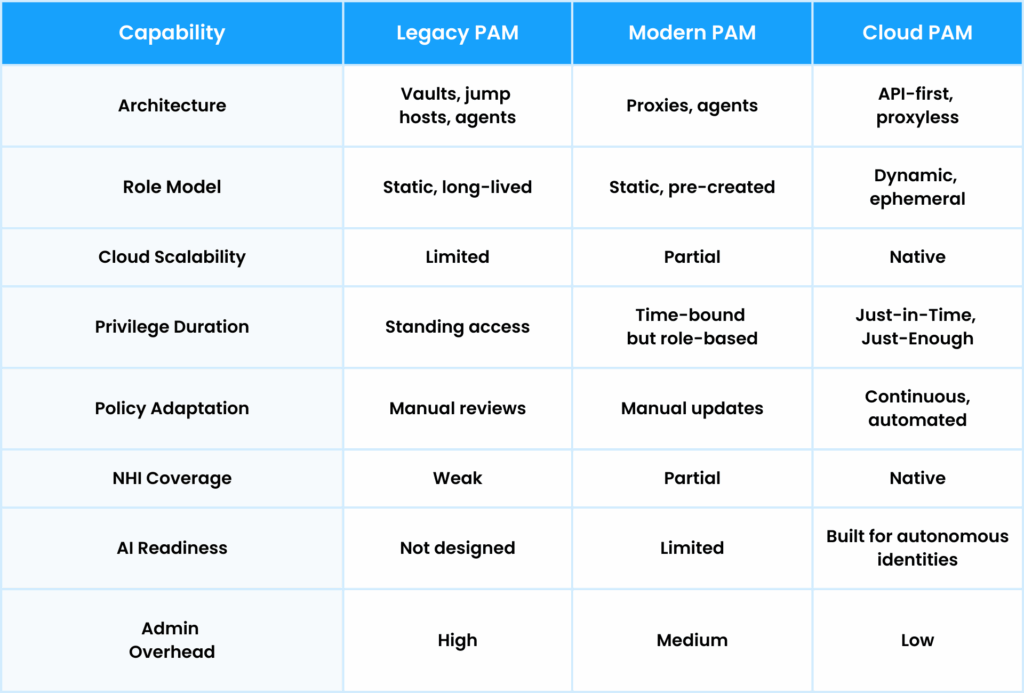
Legacy PAM vs Modern PAM vs Cloud PAM
Below is a high-level comparison of how these approaches differ. This table is meant to frame the discussion, not replace deeper evaluation.
Why Platformization Is Not Always the Best Answer
There is a natural pull toward platforms. A single vendor, a single contract, fewer integrations. In theory, this simplifies life.
In practice, platformization comes with trade-offs that are worth considering, especially after an acquisition:
- Best-of-breed capabilities are often diluted in favor of broad coverage
- Innovation slows as features compete for platform priority
- Customer feedback loops lengthen
- Product responsiveness can suffer
Ironically, these are often the same reasons the startup was attractive in the first place.
For security leaders, the question is not whether platforms are good or bad. It is whether a platform-centric roadmap aligns with the access challenges you are actively facing.
What to Look for When Re-Evaluating Your PAM Strategy
As organizations reassess their PAM approach, a few themes consistently surface:
- Can access decisions adapt continuously as context changes?
- Are privileges scoped dynamically per task, not per role?
- Is access enforced directly through cloud APIs?
- Does the model reduce operational overhead instead of shifting it?
- Can the same approach govern humans, non-humans, and AI?
These are not theoretical questions. They determine whether access becomes an enabler or a bottleneck as environments continue to evolve.
How Apono Approaches Cloud Privileged Access
At Apono, we start from a simple premise. Access decisions cannot be static in environments that change constantly.
Rather than managing large catalogs of pre-defined roles, we generate tightly scoped permissions on demand and remove them automatically when the task is complete. Access policies are driven by risk and real-time context, not assumptions made weeks or months earlier.
Our approach focuses on:
- Continuous, context-aware access enforcement
- Dynamic role creation that eliminates standing privileges
- Automated policy adaptation as resources and usage change
- Consistent governance across humans, non-human identities, and AI
Because the model is built around risk rather than identity type, it extends naturally to Agentic AI without introducing separate control frameworks or manual processes.
Turning Consolidation Into a Strategic Advantage
Vendor acquisitions are a reality of the security market. They can bring stability, scale, and resources. They can also create moments where customers pause and reassess.
If your PAM vendor has been acquired, this isn’t a crisis. It’s an opportunity to step back and ask whether your access strategy is aligned with where your organization is going — not just where it’s been.
Identity security today isn’t about quarterly reviews or static roles. It’s about continuous enforcement that can keep up with cloud infrastructure, non-human identities, and increasingly automated access patterns.
Before committing to a new roadmap or long-term contract, it’s worth pressure-testing your requirements against how access actually behaves in modern environments — and what recent consolidation signals about where the market is heading.
Our PAM Buyer Guide was created for security and engineering leaders navigating this exact moment.
It outlines what to evaluate when reviewing PAM strategy today, including cloud access models, non-human identities, and AI-driven access — and where legacy assumptions often break down.
Download the PAM Buyer Guide to ground your decision in the right criteria, or book a demo if you want to see how cloud-native privileged access works in practice.