Top 10 Identity Governance and Administration Solutions

The Apono Team
March 19, 2026
In most organizations, identity governance and administration (IGA) solutions are supposed to answer one simple question: who has access to what, when, and why? But in cloud-native teams shipping daily, that question gets messy fast. Permissions sprawl and temporary access quietly become permanent.
The blast radius is colossal. Third-party involvement in breaches doubled to 30% over the last year, which is exactly what happens when access decisions are scattered across vendors, apps, and infrastructure.
IGA still matters for compliance frameworks like SOC 2 and GDPR. Auditors expect provable least privilege and evidence you can actually trust. While many legacy identity governance and administration tools were built for slower environments, modern teams need governance that keeps up in real time. Automated, time-bound access that supports developer velocity is the way to go.
What are identity governance and administration solutions?
Identity governance and administration (IGA) solutions are platforms that define and enforce who should have access to systems and data across an organization.
IGA helps security and IT teams understand who has access, what they can do, why they have it, and whether that access is still appropriate. Nowadays, these insights extend beyond human users to service accounts and other non-human identities (NHIs).
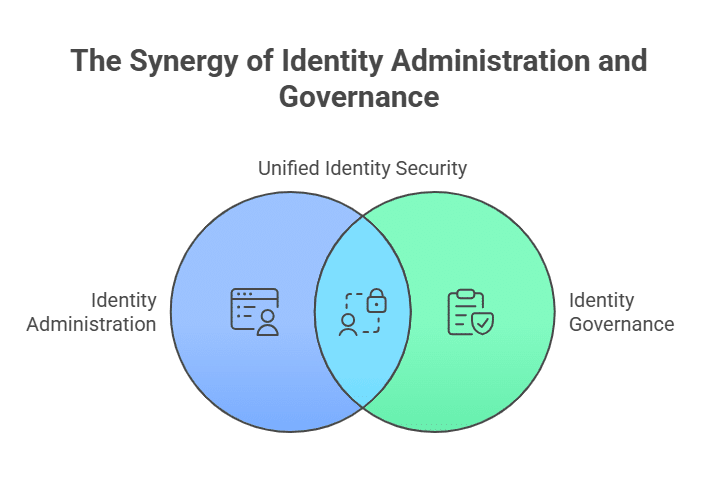
IGA has two connected pillars:
- Identity administration: Provisioning and deprovisioning access as people join, change roles, or leave, plus managing entitlement across cloud and data systems.
- Identity governance: Enforcing policy, such as least privilege and access reviews, and producing audit evidence that stands up to frameworks like CCPA.
The challenge is that many organizations treat governance as a periodic checkbox exercise, through initiatives like quarterly reviews. In cloud-native environments, access changes daily, and privileged permissions can spread fast.
That’s why modern IGA is shifting from review-and-report to continuous enforcement. Automation and time-bound access are keeping governance aligned with how DevOps teams actually work.
Types of Identity Governance and Administration Solutions
Identity governance and administration solutions aren’t one-size-fits-all. Some platforms are built for HR-driven identity lifecycle and compliance reporting, while others focus on controlling privileged access in cloud environments. Different approaches to IGA can also change how well you reduce exposure to cyber attacks.
Legacy IGA Platforms
These are the classic enterprise IGA suites designed around centralized directories and on-prem apps. They typically excel at onboarding and offboarding workflows and role modeling. The tradeoff is that they often rely on static roles and periodic reviews, which can lag behind how cloud permissions and DevOps environments actually change day to day.
Role-Based and Policy-Driven IGA
This category emphasizes enforcing access through RBAC (role-based access control) and policy-based rules like segregation of duties (SoD) and approval requirements. This approach works well in structured environments, but it can struggle when teams need highly granular, short-lived access to dynamic resources.
Cloud-Native and DevOps-First Governance
Cloud-native IGA solutions are designed for modern stacks, including Kubernetes, data platforms, CI/CD tooling, and SaaS apps, where permissions change constantly. Instead of treating governance as a quarterly “review,” these tools lean into continuous controls such as:
- Just-in-time (JIT) access
- Time-bound permissions
- Context-aware approvals
- Automated revocation
This is the direction most high-velocity engineering organizations are moving because it reduces standing privilege without turning access into a ticketing bottleneck. That shift matters because static access creates continuous threat exposure in fast-changing environments and permissions drift.
Access Review and Compliance-Focused Tools
Some IGA solutions skew heavily toward audit readiness, including access reviews and evidence collection for SOC 2 and similar requirements. They can be effective for proving governance, but may not provide strong real-time enforcement.
Benefits of Identity Governance and Administration Solutions
- Reduce identity-based security risk: IGA limits over-privileged access and helps prevent insider misuse and credential compromise from turning into full-blown incidents, strengthening your overall cloud data security posture.
- Enforce least-privilege access at scale: It gives you a consistent way to grant access, with permissions that actually match what someone needs for a specific role and environment.
- Improve visibility into who has access to what: Instead of guessing who has access to what, you get a current, reliable view of entitlements, so you can spot access sprawl.
- Support compliance and audit readiness: Strong identity controls are foundational to enforcing your broader data governance policy, ensuring only authorized users can access regulated or sensitive data.
- Standardize access processes and reduce friction: Clear, repeatable workflows mean fewer one-off exceptions and fewer tickets bouncing between teams.
- Improve operational efficiency: Automated provisioning and deprovisioning reduce manual work and help prevent orphaned access when someone changes roles or leaves.
Key Features to Look For in an Identity Governance and Administration Solution
- JIT and time-bound access controls: Make sure the tool can grant access only when it’s actually needed, expire it automatically, and still support urgent break-glass workflows.
- Automated provisioning and deprovisioning: Access should be provisioned when someone joins and revoked immediately when they leave. Bonus points if the tool can handle contractors and service accounts cleanly, not just full-time employees.
- Granular, least-privilege permissions: You want the ability to scope access tightly (by resource or environment) so people don’t end up with broad permissions just to get the job done.
- Self-service access requests: Look for workflows that let engineers request what they need without opening tickets, while still enforcing policy and applying access automatically.
- Context-aware approval workflows: Approvals should route intelligently based on what’s happening, from on-call status to ticket references.
- Comprehensive audit logs and compliance reporting: You need clean, defensible logs that show who accessed what, when, for how long, and why, plus reports you can export and map directly to audit requirements.
10 Top Identity Governance and Administration Solutions
1. Apono
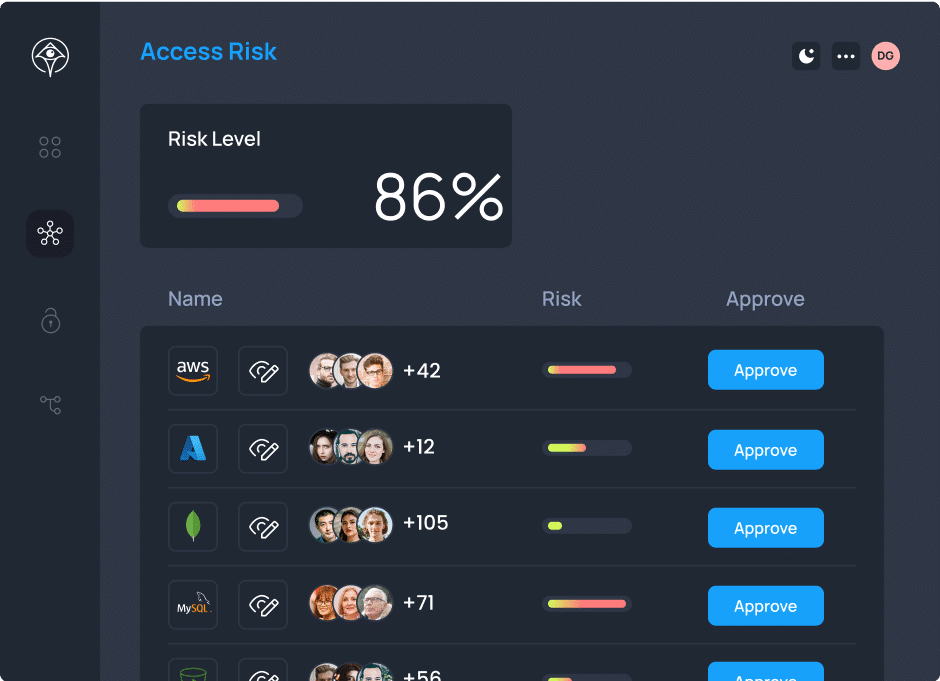
Most legacy IGA platforms were built around static roles. That model breaks down in cloud-native environments where access changes daily and privileged permissions spread silently across infrastructure, CI/CD, data stores, and third-party tools.
Apono is a cloud-native access management and governance platform built for modern infrastructure teams that need real-time control. Instead of relying on static roles and periodic access reviews, Apono enforces JIT, time-bound permissions across cloud infrastructure, apps, and data, so teams can reduce standing privilege without slowing developers down.
Main features:
- Automated JIT access with auto-expiring permissions to eliminate standing privileges.
- Auto-expiring permissions to ensure access never outlives its purpose.
- Self-serve access requests with built-in approvals via Slack, Teams, or CLI.
- Granular, least-privilege scoping to eliminate standing privileges.
- Pre-configured break-glass and on-call flows for fast incident response.
- Comprehensive audit trails showing who accessed what, when, for how long, and why.
Pricing: Contact the Apono team for tailored pricing.
Best for: Cloud-native SaaS organizations and regulated enterprises that need to enforce least privilege continuously across infrastructure, production systems, and non-human identities, without slowing developers down.
Review: “Most integration configurations are straightforward and backed up by informative yet simple documentation. In more complicated cases, Apono’s team were happy to help and solved issues fast and with high professionalism. The product supports many services and has an intuitive UI, both on the administrative and user sides.”
2. SailPoint Identity Security Cloud
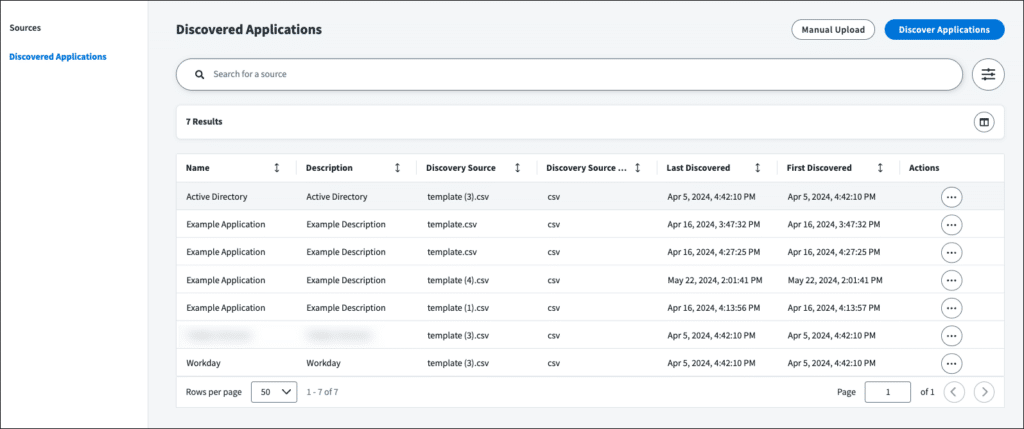
SailPoint’s Identity Security Cloud is built to help large organizations govern access across complex, hybrid environments. It uses automation and analytics designed to reduce risk while keeping access processes consistent at scale.
Main features:
- Identity lifecycle governance across users and applications.
- Automation and intelligence to drive access decisions.
- Compliance-oriented controls that support audit readiness.
Pricing: By inquiry.
Best for: A mature IGA platform with broad coverage.
Review: “SailPoint modernizes our identity management, enabling us to onboard 60 applications easily and automate HRMS tasks.”
3. One Identity Manager
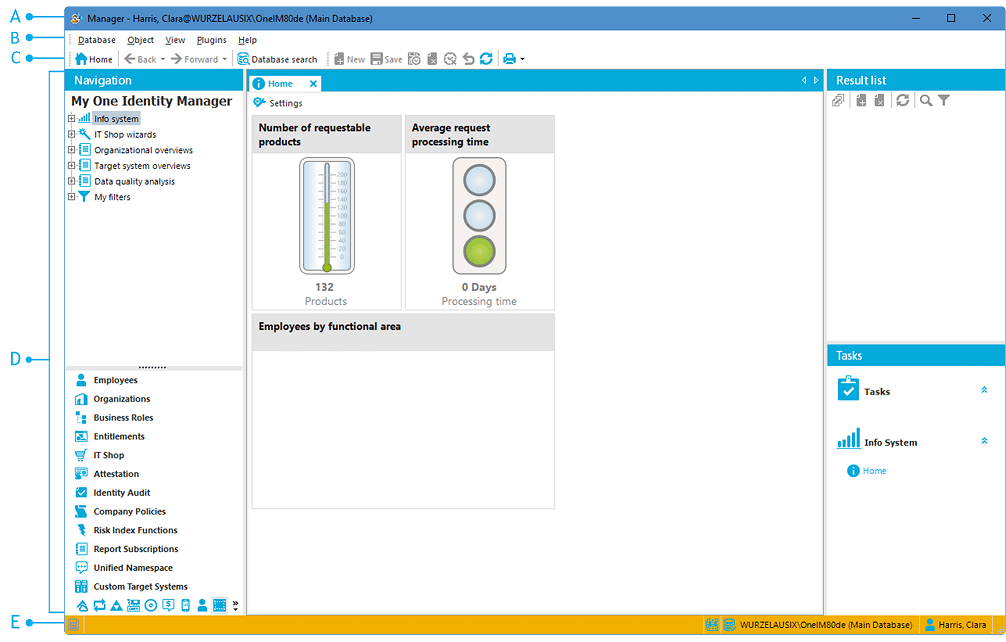
Built for organizations that need structured lifecycle management and policy-driven controls, One Identity Manager is useful where identity processes are tightly tied to business workflows and compliance requirements.
Main features:
- Governance workflows for access requests and approvals.
- Attestation and recertification support to help meet audit and compliance expectations.
- Identity lifecycle management to provision and deprovision access.
Pricing: By inquiry.
Best for: Enterprises with hybrid identity estates, i.e., a mix of legacy apps, cloud, and privileged accounts.
Review: “The initial deployment of the solution and basic level configuration required to make the system run are fairly easy as compared with other solutions.”
4. Open IAM
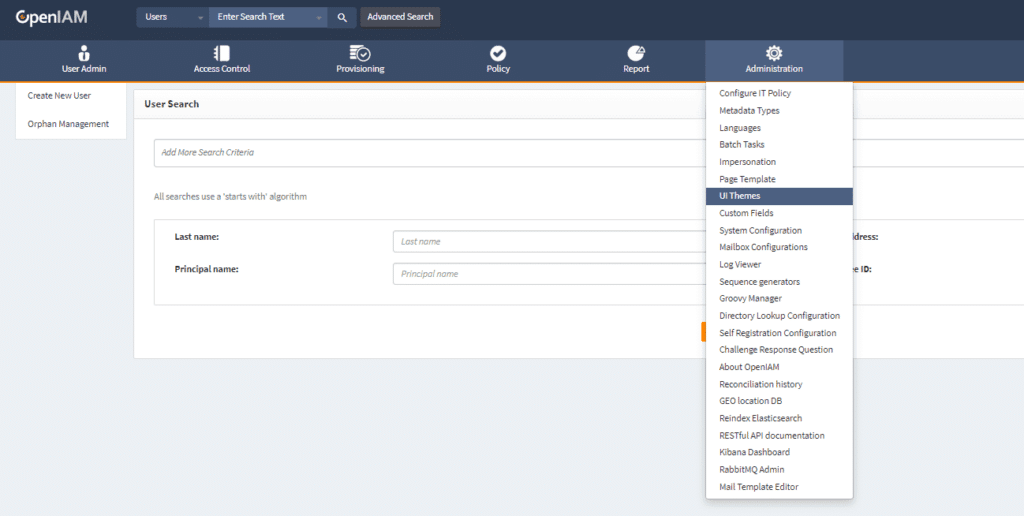
OpenIAM is a converged identity platform that includes IGA capabilities like SSO and MFA. It’s a popular option for teams that want governance controls while also retaining the flexibility of an open-source model.
Main features:
- Automated access reviews and least privilege enforcement.
- Deployment flexibility and extensive documentation for integrations.
- Subscription support tiers for the enterprise edition.
Pricing: The Community Edition is free to deploy, and the Enterprise requires an annual subscription.
Best for: An IGA platform with open source roots and deployment flexibility.
Review: “Simplified single-click provisioning and de-provisioning of users, along with great security controls and logging of who is accessing what resources.”
5. Omada Identity
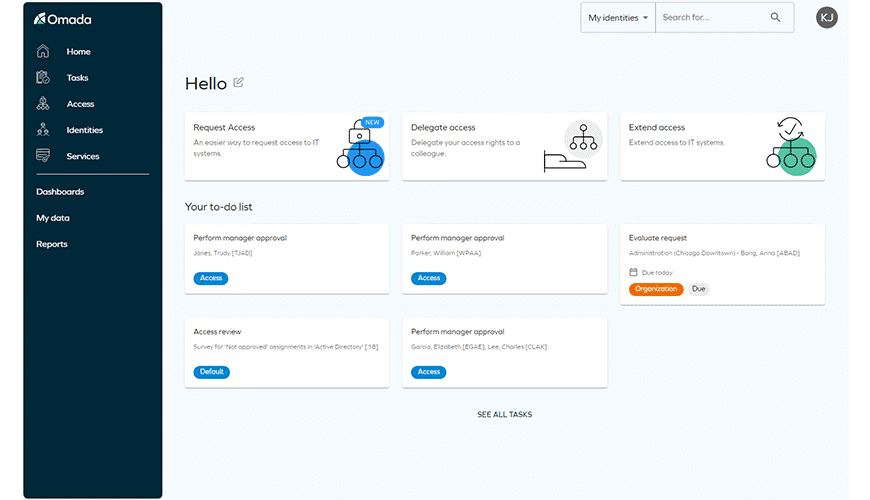
Omada’s offering focuses on unifying lifecycle management, access requests, access certifications, and reporting in a single governance framework. It’s often evaluated by enterprises that want structured identity processes with strong compliance support,
Main features:
- Intelligent compliance dashboards with remediation actions.
- HR-triggered provisioning and deprovisioning across connected systems.
- Detection and prevention of conflicting access rights.
Pricing: By inquiry.
Best for: Formal IAM and IGA programs that need structured governance across hybrid IT.
Review: “I love the clean interface, simplicity of features and controls, and how quick it is to edit user permissions.”
6. EmpowerID
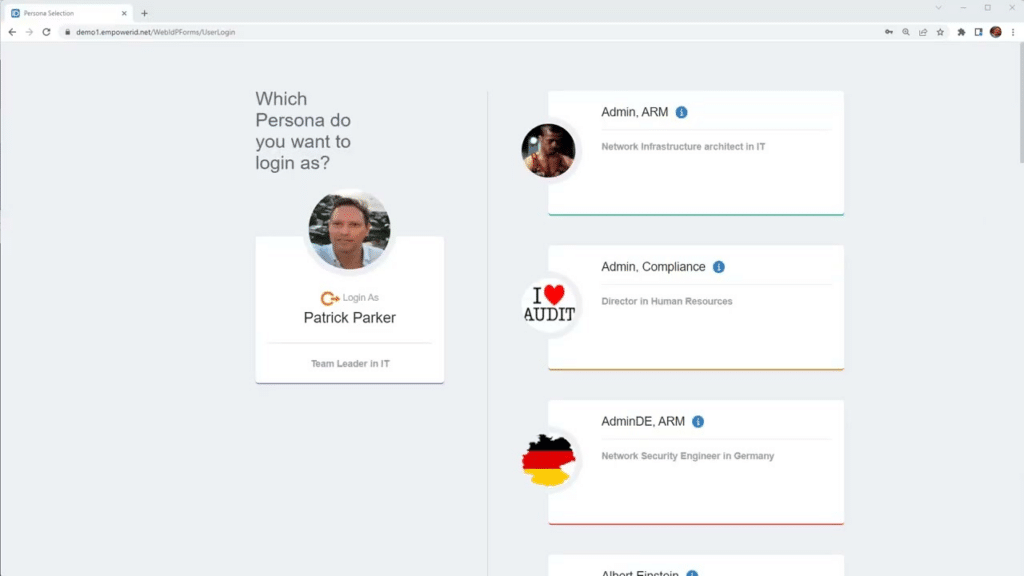
EmpowerID combines identity lifecycle management and privileged access controls in a single suite. It’s designed for enterprises that want centralized identity orchestration across on-prem, cloud, and hybrid environments, with strong workflow automation.
Main features:
- Scheduled and ad-hoc attestation campaigns with reviewer tracking.
- Centralized reporting dashboards showing access assignments and approval history.
- Event-driven lifecycle automation triggered by HR systems.
Pricing: By inquiry.
Best for: Unified identity platform combining IGA and workflow automation.
Review: “It’s a cool platform for identity management for different accounts, policies, and access compliance.”
7. Netwrix
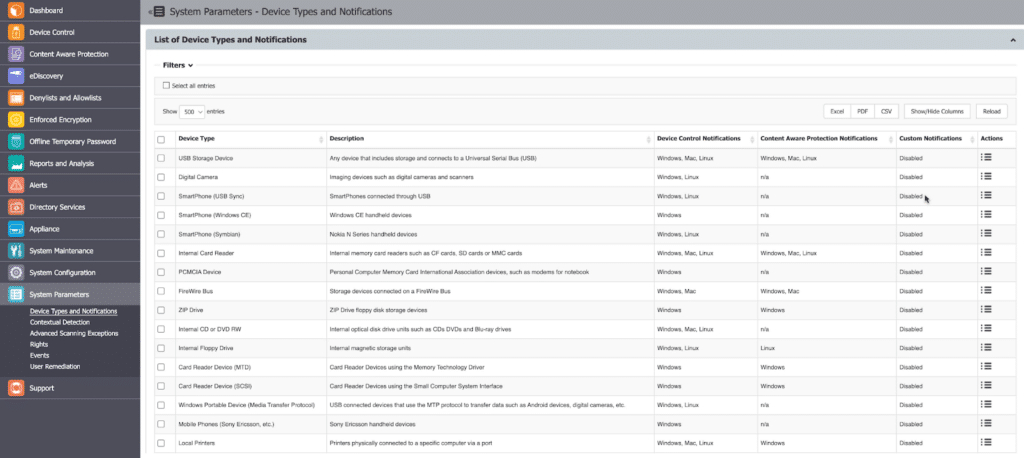
Netwrix is best known for governing and auditing access in hybrid environments, especially around directories and entitlements. For IGA, the core offering is Netwrix Identity Manager, with complementary governance coverage via Netwrix GroupID for group governance.
Main features:
- AI-assisted role modeling and centralized identity repository.
- Access Reviews workflow (via Netwrix Auditor integration).
- RBAC for lifecycle-driven provisioning and deprovisioning.
Pricing: By inquiry.
Best for: Organizations with hybrid identity and data estates.
Review: “[The] features are extensive, related to most of the use cases [for] group management. No other tool offers such [a] capability in [the] market. [The] product is flexible.”
8. WALLIX
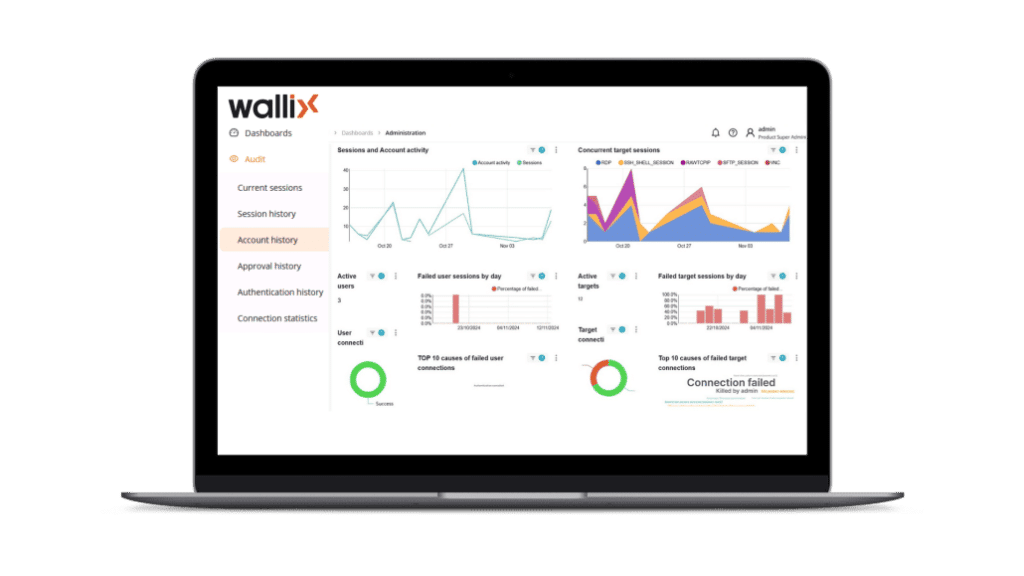
WALLIX is primarily a Privileged Access Management (PAM) vendor (rather than a classic HR-driven IGA suite). In an IGA program, it’s most useful for governing privileged access, especially for third parties accessing critical IT and OT systems.
Main features:
- Privileged session brokering and monitoring
- Vendor and remove privileged access (VPN-less portal options).
- Credential controls, including vaulting and rotation patterns.
Pricing: By inquiry.
Best for: Weak session oversight and strong monitoring and evidence.
Review: “Flexible and easy to configure monitoring of privileged access. Too [many] accounts to configure during the process of bastion installation.”
9. Ping Identity
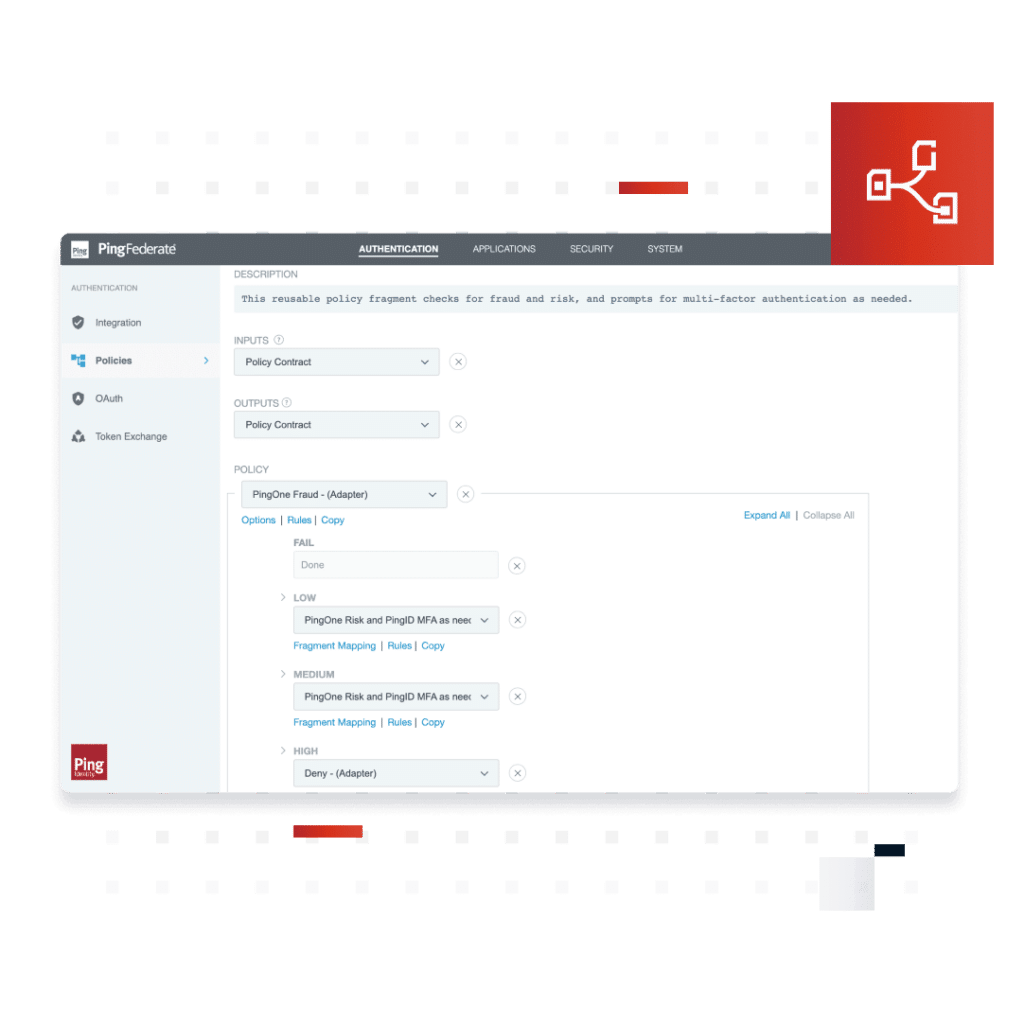
Ping Identity is an enterprise IAM platform that spans Single Sign On (SSO) and multi-factor authentication (MFA). For IGA use cases, Ping’s strength is combining access requests and governance workflows, useful if you’re standardizing identity across the workforce or customer-facing apps.
Main features:
- PingOne Authorize for centralized, policy-driven authorization.
- Access requests with configurable request types.
- PingOne Identity Governance to centrally manage identities and access to resources.
Pricing: By inquiry.
Best for: A single identity platform for SSO and MFA.
Review: “This is a cloud-based identity and access management that provides a secure and scalable solution for managing user identities and access in our internal tools.”
10. Microsoft Entra ID
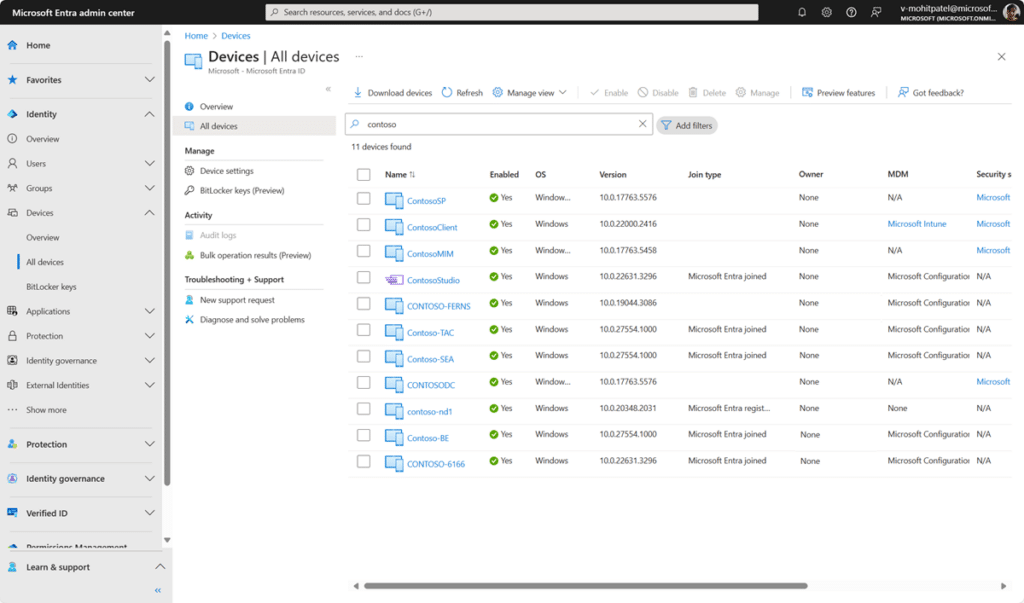
Microsoft Entra ID is an identity layer for SSO and conditional access. When you add Entra ID Governance, it becomes a practical IGA option for organizations that want access packages and lifecycle workflows in the same ecosystem.
Main features:
- Risk- and context-based policies that gate access rather than relying on static allow lists.
- Schedule recurring or ad-hoc reviews.
- Automated lifecycle workflows.
Pricing: Plans starting from $6/user/month.
Best for: Microsoft-centric enterprises that want identity security and governance.
Review: “Microsoft Entra ID has all [the] features required to build a successful end-to-end solution that can scale with the increase of our product demand grows.”
Govern Access Without Slowing Engineers Down
Identity governance is about the way you govern access to match how your teams ship. Legacy identity governance and administration tools can still help with lifecycle workflows and audit reporting, but they often struggle when permissions change daily across cloud, Kubernetes, data platforms, and third-party tools.
The best IGA solution brings together time-bound access, tighter approvals, and audit evidence you can trust, without turning every request into a ticket.
If you’re trying to modernize governance for cloud-native infrastructure, Apono enforces least privilege in real time with automated Just-In-Time access and self-serve approvals in Slack, Teams, or CLI. Download the audit readiness checklist for access and privileged access controls to see where your current governance model stands, and how to close gaps before your next audit. Alternatively, book a demo to see how Apono enforces real-time, time-bound access across cloud infrastructure, apps, and data.