10 Essential Tips For Cloud Identity Management

The Apono Team
February 26, 2026

A handful of services quietly redeploy. No one directly manages the traditional network perimeter. But somewhere along the way, an API key ends up in the wrong place. The reality of modern cloud security is that new identities are created fast, and permissions are granted broadly to keep things moving.
Over time, these permissions collect unused rights and drift away from least privilege. APIs get abused through over-privileged identities, long-lived credentials, and permissions nobody remembers approving.
In fact, the numbers reflect what many teams already feel. 57% of organizations experienced an API-related data breach in the past two years, and 73% of those victims suffered three or more incidents. Modern cloud identity management can’t stop at human users. It must treat non-human identities with the same context and Zero Trust mindset, because nowadays, they’re the ones doing most of the work.
What is cloud identity management?
Cloud identity management is the process of controlling who and what can access cloud resources, under what conditions, and for how long.
It covers both authentication (proving an identity) and authorization (what that identity can do) across cloud platforms, SaaS apps, APIs, and infrastructure. Unlike on-premises IAM, where servers and users tend to remain stable, cloud environments change constantly.
Static roles and quarterly reviews don’t cut it. Identity and access management needs to be driven by policy and enforced as things happen. The challenge is that most activity in the cloud comes from non-human identities (NHIs), such as service accounts, workload roles (including Kubernetes service accounts), API tokens, and CI/CD identities. They’re easy to over-provision and often never cleaned up. Unlike humans, NHIs cannot perform Multi-Factor Authentication. If an API key for an NHI is stolen, the attacker has immediate access.
It’s also how permission sprawl sneaks in. A CI/CD job is granted broad permissions to ship something once, and months later, it’s still running with the same access (even though nobody has thought about that project in ages).
When you manage cloud identity well, access becomes time-bound, contextual, and auditable. The goal is straightforward: enforce least privilege continuously, and make elevated access expire by default.
Why should you prioritise cloud identity management?
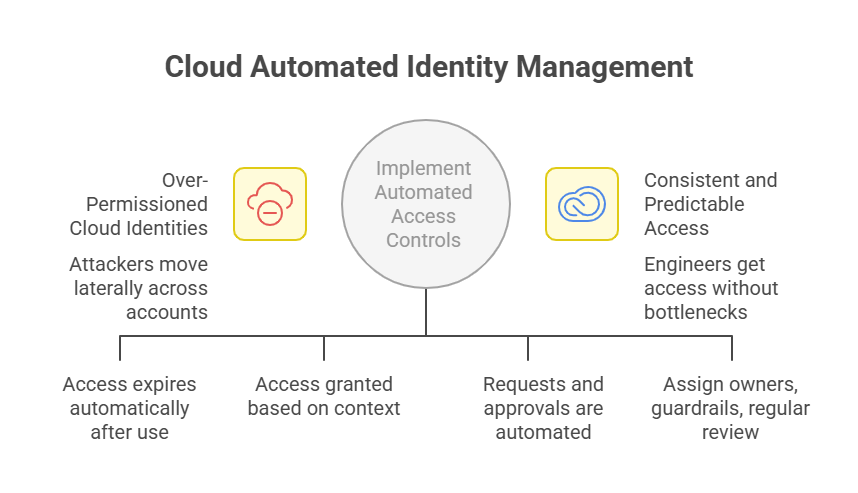
As cloud environments sprawl across accounts, services, and pipelines, identity becomes the easiest way in. Once inside, attackers often use over-permissioned identities to move laterally across cloud accounts. Long-lived access keys and static workload roles make this especially dangerous. Compromised credentials may remain valid for months without detection, which underscores the value of protecting CI/CD pipelines.
Getting rid of standing access matters more than betting you’ll never leak a key. The problem is, most teams still manage access through tickets and manual approvals. DevOps becomes the bottleneck, and people start taking shortcuts just to ship.
A big part of the mess comes from NHIs. CI jobs, bots, API keys, and workload roles are often given “temporary” access to unblock work, but the permissions remain because nobody owns the cleanup. If you want identity controls that actually hold up at cloud scale, NHIs need owners, guardrails, and regular review just like human users. In offensive security, non-human identities are especially attractive targets because they often carry broad, unattended access.
The better model is time-bound, contextual access that’s easy to audit. When requests and approvals are automated with clear policies, access becomes consistent and predictable. Engineers get what they need without turning security into a ticket queue.
10 Best Practices for Cloud Identity Management
1. Start With Centralized Visibility Across All Identities (Human + Machine)
There is a saying that goes “you can’t secure what you can’t see.” In most cloud environments, identity data is typically fragmented across cloud providers, SaaS tools, CI/CD systems, and internal platforms. Human users are only a small part of the picture.
Centralizing identity visibility brings all identities into a single control plane, making it clear who or what has access to which resources, and why. This clarity forms the very foundation of detecting over-privilege, identifying dormant access, and responding quickly when something appears to be wrong. Unlike spreadsheet-based access tracking, centralized visibility gives you real-time answers.
You can implement centralized identity visibility by creating an inventory of all human users and NHIs and assigning ownership to each. Inventory should pull data from cloud IAM systems, Kubernetes clusters, CI/CD platforms, SaaS tools, and secrets managers. With this data, you’ll be able to flag unused permissions and continuously monitor for newly created identities.
2. Replace Standing Privileges With Just-In-Time Access
Standing access may be convenient, but it’s also one of the biggest sources of risk in cloud environments. Long-lived permissions dramatically increase blast radius when credentials are compromised.
Just-in-time (JIT) access flips the model on its head. Permissions are granted only when needed and expire automatically. JIT relies on short-lived credentials rather than static keys, reducing the window of exposure if access is misused.
You can reduce the attack surface by default while also aligning with zero-trust principles. Cloud-native access management platforms make time-bound access the norm rather than an exception.
The same model applies to non-human identities, such as CI jobs and workload roles. Rather than “permanent admin just in case,” JIT makes elevated access an exception with an expiration time.
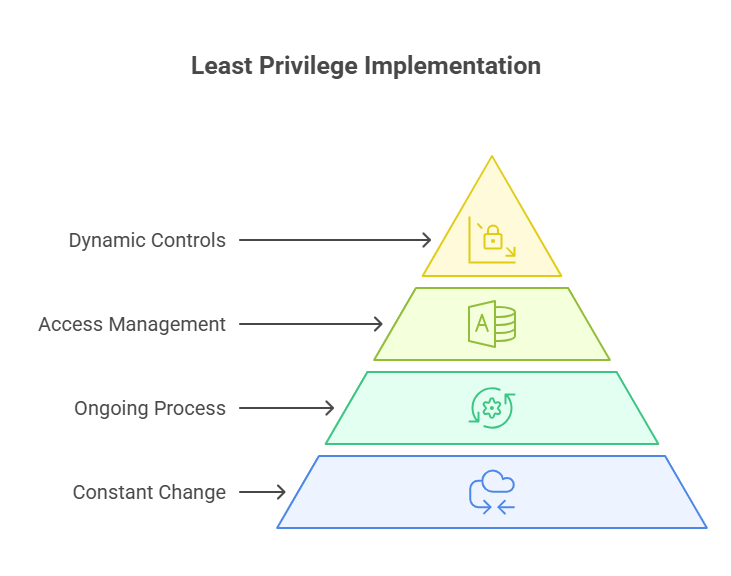
3. Implement Least Privilege as a Continuous Process
You do not “finish” least privilege. Cloud environments are constantly evolving, and their access requirements change accordingly. Hence, high-performing teams treat least privilege as an ongoing process as part of a Zero Trust operating model.
Cloud native access management platforms make refining policies and adjusting permissions manageable. Time-bound and context-aware controls keep least privilege current as infrastructure changes.
4. Automate Access Workflows to Remove Manual Bottlenecks
Manual access approvals slow everyone down. There are tickets piling up, engineers waiting in line, and security teams gatekeeping rather than partnering.
Automated access workflows remove this friction. All it takes is policy-driven approvals and self-service requests to get engineers the access they need without bypassing controls.
As a solution, Apono enables this through native integrations with tools like Slack, Microsoft Teams, and CLI workflows, so access requests fit naturally into how teams already work. Compared to ticket queues, self-serve workflows are faster and easier to govern.
5. Enforce Contextual Access Policies Based on Role, Environment, and Risk
Not all access requests carry the same risk. Risk signals may include unusual access times, unfamiliar locations, untrusted devices, or requests targeting production resources.
For example, production access should be stricter than staging. On-call engineers shouldn’t be evaluated the same way as interns.
Context-aware policies use role, environment, time, and risk signals to decide what’s allowed. That keeps controls strong where they matter, without slowing work everywhere else.
6. Secure and Right-Size Access for Non-Human Identities
Non-human identities now dominate cloud environments, and they’re often the least controlled. Static permissions assigned to workload identities become dangerous as systems evolve.
It’s vital to onboard non-human identities with fine-grained, time-bound entitlements. Workload identities receive only the permissions they need, only when they need them. This best practice significantly reduces long-term exposure while preserving automation.
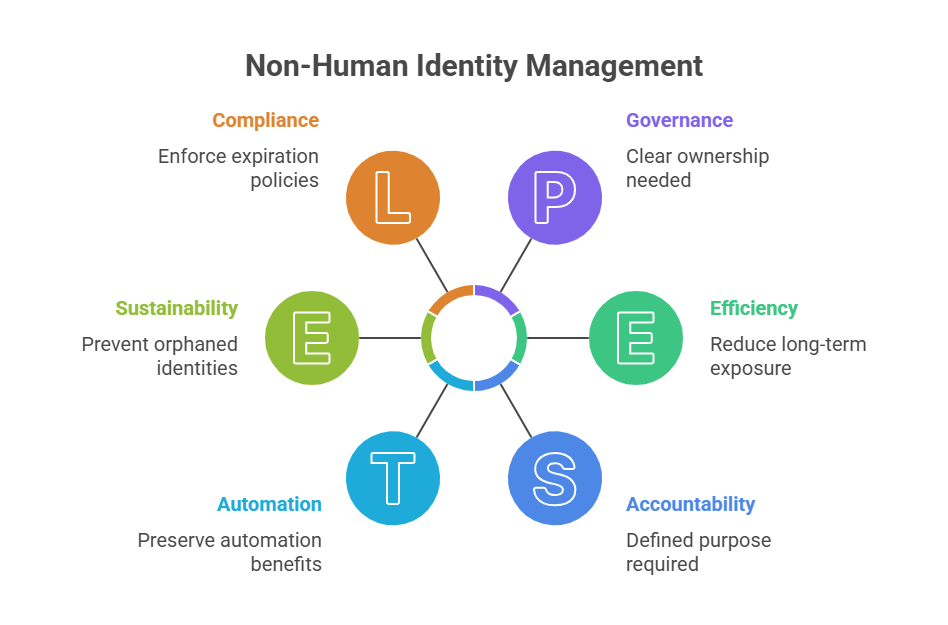
Every non-human identity should have a clear owner, defined purpose, and expiration policy. Permissions should be reviewed whenever pipelines change or services are decommissioned to prevent orphaned identities from persisting indefinitely. Treat NHIs like production infrastructure: provision, monitor, rotate, and retire on purpose; NHI management makes the biggest difference here.
7. Integrate Access Management Directly Into Developer Workflows
Security controls that live outside developer workflows are often ignored or bypassed. Effective cloud identity management meets developers where they are.
Cloud-native integrations and API-driven access controls allow identity governance to scale alongside infrastructure automation. When access requests, approvals, and audits are integrated into CI/CD pipelines and chat tools, compliance becomes a natural byproduct of normal work, rather than an additional task.
The most effective implementation best practice is to enforce identity policies directly within CI/CD pipelines, ensuring that access decisions align with deployment automation.
8. Use Break-Glass and On-Call Flows for Controlled Emergency Access
Emergencies happen. The goal isn’t to block access, but to control it. Break-glass access allows engineers to respond quickly during incidents while maintaining accountability. Well-designed on-call and emergency flows ensure access is temporary, logged, and reviewed after the fact. This best practice strikes a balance between speed and governance. Break-glass keeps emergency access fast, scoped, and auditable.
9. Continuously Audit Permissions and Monitor for Drift
Without automation, permissions drift is inevitable. Continuous auditing keeps access aligned with policy over time. Audit logs should capture who requested access, why it was approved, what changed, and when access expired or was revoked. Taking these steps simplifies the collection process for audits such as SOC 2, GDPR, HIPAA, and CCPA.
10. Apply Zero-Trust Principles Across All Cloud Environments
Zero Trust should be viewed as an operating model, rather than a product, where every request is treated as untrusted until proven otherwise. Zero-trust verification should be continuous, incorporating identity, device, and workload trust, as well as real-time risk signals.
Every access request must be verified, scoped, and time-bound, regardless of its origin. Applying zero-trust principles across multi-cloud and SaaS environments ensures identity remains the security perimeter everywhere, not just on paper. This approach reflects the shift beyond the traditional perimeter, where every request is evaluated on context rather than network location. When combined with automation and visibility, Zero Trust strengthens security without slowing teams down.
Where Identity-First Security Becomes Operational
Cloud security doesn’t fail because teams don’t care. It fails because identity has outgrown the tools and processes built to manage it.
Human and non-human identities now drive every deployment, every API call, and every production change. Treating access as static infrastructure in a dynamic cloud is no longer defensible.
Apono was designed to solve this gap between cloud scale and access control. By automating just-in-time access, eliminating standing permissions, and applying zero-trust principles across human and non-human identities, Apono helps teams regain control of cloud access without slowing engineers down. That means fewer tickets, fewer permanent privileges, and cleaner audit trails by default.
Ready to eliminate standing access, reduce identity risk, and keep developers moving fast? Book a demo with Apono and see how cloud-native, just-in-time access works in under 15 minutes.