Apono vs Entra ID PIM: Building Privileged Access Engineers Will Actually Use Across Cloud

Gabriel Avner
April 2, 2026
Microsoft Entra ID Privileged Identity Management is designed to bring structure to privileged access inside Microsoft environments. It allows organizations to make roles eligible, require activation, and enforce approval workflows.
Within Azure, it performs that role predictably.
The challenge begins when engineering workflows extend beyond Azure.
Modern infrastructure rarely lives in a single ecosystem. Teams operate across additional clouds like AWS and Google Cloud, Kubernetes, SaaS platforms, databases, and hybrid systems. In that environment, the question shifts from whether PIM can manage activation to whether it can deliver a frictionless access experience across the full stack.
Because if access feels fragmented or slow, engineers adapt. And when engineers adapt, least privilege begins to erode as security best practices get discarded by demand for employee access and productivity.
Where DevX Friction Starts
Engineers usually know what they need to accomplish. Friction appears when they must translate that goal into the correct privileged role.
In Entra PIM environments, that translation depends on predefined Azure roles that are made eligible. Those roles must be created, scoped, and maintained ahead of time.
For engineers, friction often surfaces in familiar ways:
- Not knowing which eligible role maps to the task
- Activating a role only to discover it does not provide needed access to required assets.
- Waiting for role activation during time-sensitive work (5-45 min delays)
- Switching between cloud consoles to complete a single task
These issues are manageable in isolation. Repeated often enough, they influence behavior.
If the right role is unclear, engineers may request broader eligibility to avoid getting blocked. If activation delays interrupt debugging or incident response, certainty begins to outweigh precision.
That drift does not start with policy failure. It starts with workflow friction.
Where PIM’s Model Creates Structural Friction
PIM’s core model is built around eligible roles that exist in advance. Even though access is time-bound after activation, the roles themselves are static constructs that must be continuously maintained. This rarely occurs proactively.
Access is more often extended after work stoppage.
Static Roles in Dynamic Environments
Azure roles are powerful, but they must anticipate future needs.
In fast-moving cloud environments, infrastructure evolves constantly. New resources are deployed. Services span multiple clouds. Responsibilities shift between teams.
As a result, those static roles break, which creates a moving target for security and compliance teams as they try to keep role definitions aligned with evolving engineering needs. When roles are too narrow, engineers activate one role, discover it is insufficient, and request another. When roles are broadened to reduce friction, they drift away from least privilege.
Over time, patterns emerge:
- Role definitions expand to reduce repeated activation friction
- Engineers request broader eligibility to avoid delays
- Precision gives way to convenience
PIM can enforce time-bound access inside Azure, but it does not dynamically shape access in the context of the work, and where the work is being done whether that work is in Azure alone or, more typically, beyond Azure.
Fragmentation Across Clouds
PIM provides structured control inside Microsoft environments. The challenge is that most enterprises do not operate inside a single cloud.
Authentication may be centralized, but privilege enforcement often becomes fragmented. When access works one way in Azure and another way in AWS or Kubernetes, the experience becomes inconsistent.
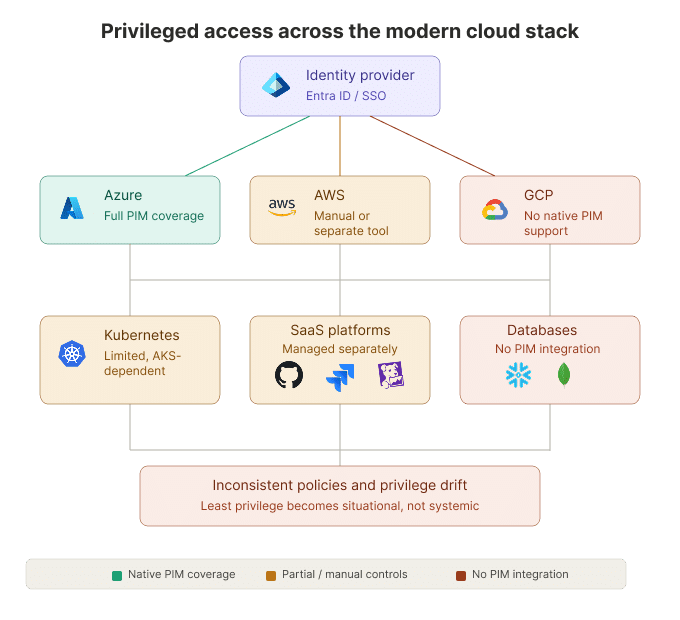
Engineers quickly learn which systems are slower or more restrictive and adjust their requests accordingly. Over time, least privilege becomes situational instead of systemic.
This is not a weakness in PIM itself. It is a limitation of using a cloud-native role system as a cross-cloud privilege model.
Workflow Expectations Have Changed
Engineering workflows have shifted. Slack, CLI, internal developer portals, and AI-driven tools are increasingly vital tools where developers spend a lot of their time.
PIM, however, is primarily console-driven. While it integrates well with Microsoft services, it does not provide native Slack-based request flows, MCP integrations, or AI-assisted guidance to help engineers determine what to request.
When engineers are unsure which role maps to their intent, the system does not guide them. They must interpret Azure role structures themselves.
When the request experience lives outside the workflow, context switching increases. During production incidents, even small delays influence behavior, and over time, engineers optimize for reliability and speed rather than tightly scoped privilege.
How Apono Aligns Access With Modern Engineering Work
Apono approaches privileged access as a unified heterogeneous control model across environments rather than a feature embedded inside a single cloud provider.
Engineers can request access through Slack, Teams, CLI, Backstage, a dedicated portal, and AI-driven interfaces including MCP integrations. The request happens inside the workflow instead of outside it, and the method does not change depending on which cloud they are operating in.
When engineers are unsure what to request, the system helps translate intent into the appropriate resource and scope. That reduces guesswork and discourages over-requesting.
Access is provisioned dynamically at runtime under defined guardrails rather than relying solely on static, pre-created roles. Privileges are available automatically in seconds, align with the task, and expire automatically when the work is done.
If work extends longer than expected, duration can be extended within policy without restarting the entire process. That reduces the incentive to request broader access up front.
Instead of expanding static roles to keep pace with change, Apono provisions access dynamically and applies consistent guardrails across Azure, AWS, Kubernetes, and SaaS environments. The request experience remains uniform regardless of where engineers are working, allowing least privilege to function as an operational reality rather than an aspirational policy.
Make the Secure Path the Fastest Path
At their core, engineers are problem solvers. If getting the right access they need to achieve their goals becomes a problem, then they will find ways around it.
It is up to security teams to put in place the tools and processes that will enable engineers to move faster without compromising on their security priorities. When requests are intuitive, guided, and time-bound by design, least privilege becomes practical instead of aspirational.
View the Apono vs. Microsoft Entra ID PIM comparison brief, or book a personalized walkthrough to see how Apono can help you build a cross-cloud access model engineers will actually want to use.